CHAPTER 25
The electron is the ultimate precision-guided weapon . . .
—DCI John Deutsch in Senate testimony, June 25, 1996
In mid-December 1991, the CIA’s Soviet/East European Division held its annual Christmas party. The mood was especially jubilant and attendees, including their OTS colleagues, received a campaign-style lapel button depicting the red Soviet hammer and sickle; beneath the red star were the words THE PARTY’S OVER.1 Without media coverage, on December 31, 1991, a small detachment of Red Army soldiers marched to the Kremlin walls and replaced the red hammer-and-sickle flag of the USSR with the Russian tricolors not seen since the 1917 revolution.2 For the CIA and OTS, their main adversary had been vanquished. A year later former DCI James Woolsey stated, “With the end of the Cold War, the great Soviet dragon was slain.” Then he wryly noted that in its place the United States faced a “bewildering variety of poisonous snakes that have been let loose in a dark jungle [and] it may have been easier to watch the dragon.”3 For CIA officers, four transnational intelligence issues had emerged as competitors for intelligence resources and alongside traditional national targets such as North Korea, Cuba, Iraq, Iran, China, and Russia. These were:
• Terrorist groups and Middle Eastern Islamic extremist cells
• Proliferation of nuclear, biological, and chemical weapons
• Criminal and narcotics-trafficking cartels
• Regional instability, particularly in Africa and the Middle East
Less widely recognized at the time was the oncoming technical revolution in intelligence as the Information Age gave way to the Information Society with the accompanying creation, distribution, diffusion, use, and manipulation of information affecting global economics, politics, and cultures.4 Digital information systems, used in the CIA for more than two decades, ceased being location specific and were now being connected and accessed throughout the world in unsecured spaces over an electronic spiderweb named the Internet. Former CIA officer James Gosler observed that because of the emergence of digital technologies in the 1990s, “the conduct of espionage had been irreversibly altered, owing in large part to the rapid expansion of global reliance on information technology.”5 These digital technologies, combined with servers, routers, and a terminal at every desk, transformed information at every level—creation, storage, processing, viewing, sharing, and transmission.6
Specialized subminiature cameras developed by OTS to photograph documents stored in a target’s filing cabinet were of limited value when computer networks became the repositories for secrets. Gosler noted, “Clandestine photography is rapidly yielding to sophisticated technical operations that exploit these networks. Spies with authorized access to these networks—an insider—can exfiltrate more than one million pages of sensitive material inside a microelectronic memory device easily concealed within a watch, an ink pen, or even a hearing aid.”7
Examples of the rapid obsolescence of Cold War collection devices can be found in some OTS equipment developed in the 1970s to support CIA agent Kuklinski in Poland, who had access to the Soviet war plans. Over the course of nine years, Kuklinski secretly photographed more than 25,000 pages of classified Soviet and Polish military planning and capabilities documents.8 OTS supplied technology for the operation that included disguises, concealment devices, subminiature cameras, suicide pills, and covert communication devices.9 Today, the technology for most of Kuklinski’s communications and specialized camera equipment is obsolete and the secret documents he photographed and dead-dropped to his case officer would likely be imaged, transmitted, and disseminated in electronic form.10
The digital revolution did not alter the CIA’s goal of clandestine collection of adversaries’ secret plans and intentions. However, the role of agents fundamentally shifted from a spy who is supported by clandestine technology to the spy who supports a clandestine technical operation.11 Spy gear had to adjust to the needs of the agent who would become an infiltrator and compromiser of computer networks rather than a reporter of information. In a sense, the technology, just like an agent, would be “recruited” to spy.
Legendary criminal Willie Sutton was once asked why he robbed banks. He responded, “Because that’s where the money is.” While some money remains in brick-and-mortar banks, the “mother lode” of wealth is now found in the financial cyberworld. The criminal skills and tools, and tradecraft possessed by a Sutton would be of little value in robbing a cyberbank. The same is true for intelligence collection. Over time, the location and form of secret information changed. Correspondingly, the skills, tools, partnerships, and culture of tradecraft have been forced to evolve.12
To uncover another country’s military, political, or economic secrets, targeting an opponent’s information technology can be exponentially more valuable than stealing paper documents. Thanks to new digital technologies, the covert transfer of vast amounts of information, or clandestine attacks on enemy networks no longer requires a physical presence, and can often be conducted remotely from anywhere on the globe using the Internet.13
Regardless of the era, sound tradecraft has always employed the best available technologies to support clandestine activities. While espionage goals and objectives remain constant, global access to digital systems and information altered time-honored methods and techniques of spying. Emerging information technologies also allowed traditional tradecraft to be applied in new ways.
The Internet and the global availability of personal database information makes the spotting of individuals with potential susceptibility to recruitment independent of geography or personal engagement. Using the Internet for assessment and as a spotting tool, intelligence services can focus on a smaller pool of potential recruits. Profession and position often indicates access to sensitive information and vulnerabilities are revealed by Internet communications and search habits.
Digital ink never fades and “private” thoughts and comments expressed in obscure publications reside permanently on the Internet as searchable public records. Whether entries are in the form of a blog, posted on a chat site, contained in a circulated e-mail, published in a book or magazine article, or transcribed from a television interview, they become available indefinitely to anyone with Internet access. Opinions and musings from one’s youth might provide tantalizing clues to a person’s beliefs, values, interests, and vulnerabilities, all of which are immensely valuable in the recruitment process.
Publicly accessible Internet databases enable the remote and anonymous aggregation of comprehensive personal and financial profiles. Types of information readily available include employment, profession, educational history, job-change patterns, health, marital status, address, social security number, driver’s license number, income, personal debts, credit card numbers, travel patterns, favorite restaurants, lawsuits, and bankruptcies.
An examination of a computer user’s database information can further reveal potential recruitment vulnerabilities. Examples include:
• Recurring purchases at a liquor store or bar might suggest problems with alcohol.
• Large expenditures at pharmacies or a hospital might reveal undisclosed health problems.
• Bankruptcy or bad credit reports could indicate financial strain.
• Travel patterns and expenditures might point to extramarital relationships.
• Frequent job changes could mask failed career expectations.
• Recreational interests in dangerous or thrill-seeking activities such as scuba diving, sky diving, or motorcycle racing, could identify a risk taker who might also be inclined to accept espionage as living even more “on the edge.”
For the recruiter of spies, Internet information becomes an efficient tool for identifying targets to develop and discarding those without access or apparent vulnerabilities.
Internet accessibility to commercial databases has made the creation of effective cover and the use of disguise more problematic. The traditional identity details of address, profession, and association membership become immediately verifiable using Google or other common search tools. Because the effectiveness of cover and disguise can erode quickly under examination, light commercial cover could be compromised by a curious hotel check-in clerk with Internet access. In the hands of a counterintelligence professional, even a well-backstopped cover can be pierced by identifying anomalies and dates involved with the created identity. Because so many details of a person’s identity are now publicly available, it is difficult to create sufficient supporting records to construct an individual’s entire life history including records of education, credit cards, residence, family, children’sschools, neighborhood associations, library cards, and driver’s licenses. The amount of information needed to legitimize identity has made sustaining a cover identity over an extended period nearly impossible if a determined adversary has the ability to exploit the Internet.
Light disguises that include fake beards, mustaches, hair coloring, hats, or scars may fool the human eye, but not a camera with face-recognition software that is linked to a database. Biometric data such as iris scans, passports with memory chips, digital fingerprinting, and electronic signature matching have all emerged as new industries for commercial security and intelligence requirements.
Digital technology offers options for concealing data in forms never possible during the Cold War. The tens of thousands of pages of sensitive information collected by Kuklinski over his nine-year spy career could be compressed and stored on a memory card much smaller than a postage stamp. Embedded computer chips in toys, cameras, digital music players, calculators, watches, automobiles, and many home consumer products make it possible to alter the memory in any device to conceal secret information. An agent no longer needs to possess compromising concealment devices for hiding film, one-time pads, secret-writing chemicals, and escape instructions, since all of that information can be stored electronically in everyday devices that defy detection. The likelihood of an agent’s properly concealed digital information being detected approaches zero.
The remarkable reduction in size of microphones, transmitters, and cameras since 1991 has resulted in easier concealment, less power requirements, and use of smaller batteries with a longer operational life. Tiny collection tools such as digital video cameras and microphones, small enough to be fitted on small robotic “crawlers” the size as a common cockroach, can explore, map, and exploit air-conditioning vents, drainpipes, and ventilation shafts for surveillance. It is now possible to convert any image or sound into a digital format, which can then be encrypted and transmitted instantly across the Internet or by satellite on government or commercial communication links.
For example, advanced software recognition programs can link video images to database programs that enable the surveillant to capture real-time images of license plates to build instantly a database of all vehicles and their owners passing an observation point. Such information, over time, could reveal the identities of security and intelligence personnel involved in activities near the location. Forms of “Face Trace” programs enable video images to be rapidly compared to records in distant databases for identification.
New generations of low-cost radio-frequency identification chips created for the retail industry offer an opportunity to tag an unsuspecting target by embedding a tiny chip in clothing or the sole of a shoe. These embedded passive chips can be scanned as targets pass through electronic choke points and represent a digital version of the Soviet “spy dust.”
Astonishingly small, unmanned aerial vehicles with wingspans of less than one-half inch, carrying cameras and audio sensors, can be remotely piloted to surveil targets from above, or guided into a building to serve as a movable “flying bug.” A Defense Advanced Research Projects Agency version is small enough to fit on a thumbnail, yet capable of carrying either audio or video sensors. Ninety percent of its internal power goes toward navigation and propulsion, while 10 percent maintains the sensors. An early CIA version of the flying device from 1976, called the Insectothopter, is on display inside the Agency’s Original Headquarters Building alongside a prototype of an advanced Defense Advanced Research Projects Agency (DARPA) model no larger than a black horsefly.
Public awareness of Cold War tradecraft often focused around the communication techniques of brush passes, car tosses, and dead drops. Despite their sophistication and usefulness at the time, all of these techniques were vulnerable to surveillance by an alert counterintelligence service. In the United States, the arrests of Navy spy John Walker in 1985, and Aldrich Ames, a KGB mole inside the CIA, in 1994, were precipitated by their actions in communicating with their Soviet handlers .14
The advent of the Internet affected all of the “pillars of tradecraft,” but none more so than covcom where it revolutionized clandestine communications. Criminals and terrorists, as well as intelligence services, quickly recognized that the Internet offered unprecedented capabilities to communicate with near impunity. Messages, information, and signals were transmitted in ways that appeared innocuous and defied detection by being interlaced into the burgeoning traffic transiting the Internet. As information flowed through the “Net,” both the identity and location of the recipient and sender could be masked in a bewildering variety of disguises. A Cold War covcom plan that required weeks to plan, and was dangerous to execute, could be completed safely in seconds over the Internet. Encryption and steganography techniques using the latest advances in technology were developed to protect and conceal data in digital files transmitted globally.
The Internet allowed computer users, including bankers, criminals, merchants, terrorists, and spies, to communicate instantly and easily, from anywhere to anywhere in the wired world. The global popularity and availability of Internet services allowed users who wished to remain undetected to blend their few messages in with billions of daily e-mails and file transfers; the hard-to-find needle in the haystack became the nearly-impossible-to-track electron in terabytes of data. Intelligence agencies recognized the potential to exploit the Internet, as they had with satellites and cell phones in earlier decades. Covert use of the Internet, however, still demanded that traditional requirements for secure and nonattributable message exchange be met. The digital technology made message encryption and steganography far easier, but every successful covcom system, whether based on dead drops, SRAC, satellites, or the Internet, had to meet four conditions.15 The protection of the agent and the integrity of the operation demanded that covert communications be “SPAM” proof:
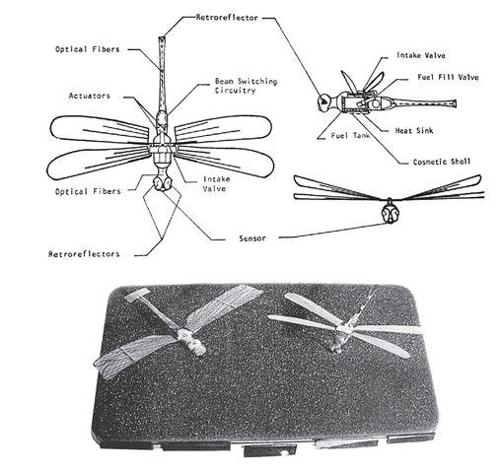
Top: Line drawing of the Insectothopter, an early CIA attempt to develop a miniature unmanned aerial vehicle, disguised as a dragonfly, for intelligence operations, circa 1976.
Bottom: Two prototypes of the flying Insectothopter created by the CIA, showing variations of wing-propulsion systems, circa 1976.
Secure: The message content must be unreadable to anyone other than the intended recipient. OTPs and software encryption are different paths to the same end—they protect the meaning of a covert message, even if it should be intercepted.16
Personal: The message presence must be inaccessible to anyone other than the intended recipient. A loaded-brick concealment and a video file loaded with digital steganography both provide a host for secret messages that would appear uninteresting and normal for their environment. Only the intended recipient would know to look inside.
Avoid traffic analysis: The existence of a communications link between the agent and handler must be hidden for the same reason that officers and agents traditionally used dead drops to preclude awareness of their covcom. There must not be any record of clandestine activity, including malicious software on the agent’s hard drive, to raise suspicions about the agent during a search.17
Mask the existence of the fact of communication: The fact that a communication is or has occurred must remain secret. Dead drop sites would be used only once and not approached by either the agent or the case officer if suspicion of surveillance existed. Covert Internet exchanges can use remailers, cutouts, public systems, and digital dead drops for a similar objective.
The two critical components in a successful covert digital communication system are the message and its method of delivery. The message is made secure using digital encryption and secret, or invisible, using digital steganography. Both communication techniques can be used separately or together—first performing the encryption and then hiding within another file to be transmitted over the Internet.
For centuries encryption that protected information was generated by humans and early mechanical ciphers were vulnerable to being broken by other clever humans. The development of the first high-level electromechanical encryption machine took place in 1918 and produced ciphers that were, at the time, “unbreakable” by the unaided human mind alone. Though the electromechanical machines produced secure cipher text, the technology was controlled by governments with an extraordinary need for secrecy. 18 In the mid-1970s, however, strong encryption algorithms began migrating from the sole preserve of government agencies into the public domain. By the 1990s, digital encryption algorithms were widely used for protecting Internet e-commerce, mobile telephone networks, and automatic teller machines. The end of the Cold War saw the development and broad distribution via the Internet of sophisticated encryption algorithms to any user anywhere.
Phil Zimmermann is credited with developing the first version of a public encryption program, PGP (Pretty Good Privacy), in 1991. He had been a longtime antinuclear activist, and created PGP encryption to provide like-minded people with secure use of computerized bulletin board systems and messages and file storage. There was no charge for the software and the complete source code was included with all copies. PGP encryption found its way onto Usenet and from there onto the Internet. From a security standpoint, there is no publicly known method to break a PGP-generated message by cryptographic, computational means. For the first time in history government-level encryption software was available for free to anyone with access to the Internet.19
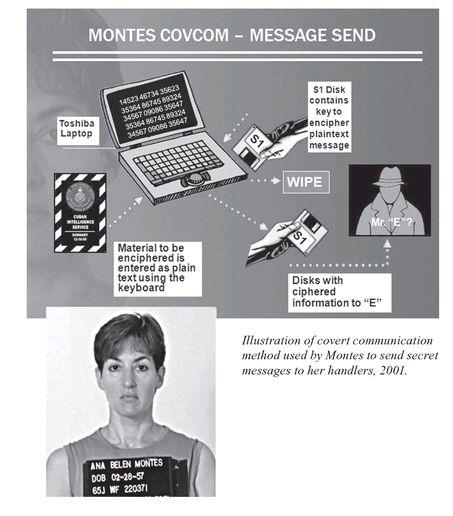
Intelligence services with limited financial resources soon adopted PGP and similar encryption software to create powerful and unbreakable agent covcom systems once available only to the major superpowers. The small, but aggressive, Cuban intelligence service used publicly available encryption software to communicate with its agents operating inside the United States. An advanced version of a PGP encryption program was discovered in September of 2001 during the search of the Washington, D.C. apartment of Ana Belen Montes. Montes, who the FBI code named BLUE WREN, was a Defense Intelligence Agency intelligence analyst for Cuban affairs, and a spy for the Cuban intelligence service.
For her covcom, Montes had been instructed to purchase a Toshiba 405CS laptop computer and was provided by her Cuban handlers, assigned to the Cuban Mission at the United Nations, with two diskettes, S-1 and R-1, for encrypting and decrypting messages. Because the possession of high-level encryption software would be alerting if Montes’s laptop computer was examined forensically, digital encryption programs (PGP or similar) and one-time keys were embedded on each diskette. When receiving messages transmitted to her Sony shortwave radio by her service, she would copy and enter the ciphertext numbers into her laptop computer and insert diskette R-1 to recover the plaintext. To prepare secret information to be handed over to the Cubans she would enter the plaintext into her laptop and then use the encryption program and key embedded on diskette S-1 to convert it into ciphertext.
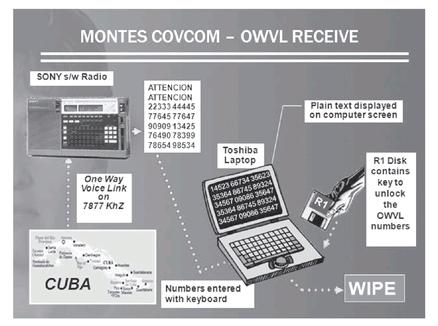
Diagram of Cuban agent Ana Belen Montes’s one-way voice system for receiving encoded messages from Cuba, 2001.
As long as Montes wiped her laptop hard drive after each covert use (to erase any trace of the process), and concealed her two special diskettes, the messages she was sending and receiving would have been virtually unbreakable. Despite her instructions, Montes did not wipe her hard drive after each use. As a result, during the FBI search of her apartment and computer, plaintext copies of her communications were recovered.20 The weakness was not in the encryption software, but with the faulty tradecraft of Montes.
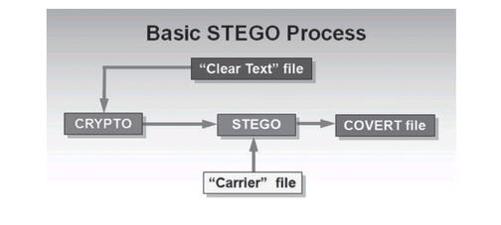
Once a message is encrypted, digital steganography can be used to hide it among the ones and zeros in any electronic transmission. Steganography, while not a form of encryption, protects messages by rendering them invisible. If the existence of a message cannot be discovered, its secrets are not revealed.
Publicly known digital techniques have made the use of steganography available to anyone to hide data and messages in virtually any electronic document and instantly send the secret information to anywhere on the globe over the Internet. Spies used limited digital techniques for hiding information during the Cold War. In the late 1980s, FBI Special Agent Robert Hanssen, a mole for the KGB, sent messages to his handlers on eight-inch floppy computer diskettes. Because the secrets he was selling would likely lead a trail back to him if discovered, Hanssen first encrypted the information and then concealed it on the diskettes using a technique called “40 track encryption.” The little-known technical process reformatted the computer diskette and allowed data to be concealed by placing it onto specific tracks on the diskette inaccessible to the computer’s internal operating system.21 While the obscure digital techniques used by Hanssen in the 1980s were known only to so-called computer geeks, by the 1990s digital steganography programs for hiding data were readily available to anyone with Internet access.
It is possible to conceal data digitally inside music or video files in ways that make them sound and appear to be unaltered. Audio files can conceal information by altering digital bits of the file that are inaudible to the human ear. Graphic images allow the redundant bits that make up the colors to be altered in a way that appears identical to the human eye.22 The secret messages are concealed within the bits of data. If someone does not have the original, or host file to serve as a comparison, the altered covert files with hidden messages can be very difficult to detect—especially so when combined with millions and millions of e-mails and file attachments that are sent daily over the Internet. Steganographic software uses an algorithm to embed data in a host image or sound file, and a password scheme for retrieving the information as illustrated in the graphic on page 454.23 Professional intelligence services may use advanced steganography programs to incorporate encryption programs for additional security in case the message should be discovered.24
Digital technology has also reformed the classic microdot technique of using tiny pieces of film less than 1 mm square to conceal a page of text. It is now possible to create and embed large quantities of digital information inside tiny e-mail electronic “dots.” Once created, “digital dots” can be concealed in a variety of unconventional methods that defy detection. Virtually any type of digital file can be modified to conceal information, rendering the counterintelligence task not one of finding a needle in one haystack, but rather that of searching millions of haystacks without even the aid of a magnet.
Dead drops were used extensively during the Cold War as hiding places for information and money exchanges between the spy and handler, but subjected both to the risk of exposure and arrest.25 Using the Internet, it becomes possible to create e-mail accounts to send and receive digital files and messages anonymously.
A secure digital dead drop e-mail account can be easily created from a personal laptop computer by anonymously signing up with an Internet service provider who offers a period of free access without requiring a credit card. From that newly created intermediate account, the user can log on to any similar service and create a second anonymous account to serve as the dead drop. Anyone can send digital files to the dead drop account and, with knowledge of the primary account password, content can be downloaded from anywhere in the world. To protect the security of the dead drop, users log on anonymously from the intermediate access account. America On Line and other Internet service providers also allow users to save an uncompleted e-mail or document onto the provider’s hard drive to be retrieved later. This feature lets conspirators possessing the primary account password communicate by retrieving and editing the stored document without ever sending it as an e-mail or attachment. Regardless of the techniques used, for greatest security, the hard drive of the laptop would be wiped after each Internet session.
The options for covert communications using digital technology appear endless and remain a persistent problem for counterintelligence. Intelligence services anonymously establish e-mail accounts under fictional individual or business names and use them to receive coded messages and digital files from sources. The e-mail addresses, similar to a postal accommodation address, have no public association with the intelligence service and if necessary can be only once and discarded. Use of such an account would not be for agents in high-risk countries, but offers a method of anonymous communication elsewhere. A simple e-mail to a “notional account” could mask a coded communication, which would be unbreakable if used only once. For example, a Cuban agent recruited abroad and returning to Havana might send a seemingly innocuous e-mail to a friend in which he discusses his passion for stamp collecting. In reality, the “friend’s” e-mail address arrives at a computer in the intelligence service and is a signal that the agent is ready to begin work. With limited use and selection of a topic consistent with the agent’s lifestyle and interests, such communications defy discovery.
An unmodified computer’s operating system leaves “tracks” that allow counterintelligence forensic specialists to recover plaintext copies of encrypted e-mails, regular e-mails, deleted files, cookies, temporary Internet files, Web site history, chat room conversations, instant messages, pictures viewed, recycle bin, and recent documents. Wiping the hard drive by permanently erasing its contents eliminates evidence of clandestine activity, but is often impractical for an agent using his business or family computer. As a solution, a covert operating system can be installed on a tiny concealable USB storage device smaller than the tip of one’s pinkie finger. When the device is connected, the computer boots from the covert operating system inside the USB without leaving a trace of its activities of the computer’s internal hard drive. The agent can then use the computer’s keyboard, monitor, printer, and Internet connection without fear of leaving a forensic trail. The covert USB system is small enough to be portable and easily concealed.
The routing of voice conversations over the Internet or through any other Internet provider-based network also creates an opportunity for clandestine communication while bypassing telephone networks. Voice Over Internet Protocol (VOIP) encryption techniques scramble the conversations to render them meaningless if intercepted. Future advances in encryption techniques offer the potential to provide secure and unbreakable voice communication. However, until encrypted VOIP communication becomes more common for businesses and individuals, the presence of such software on an agent’s computer will be alerting to a counterintelligence service.
Low-cost mobile telephones, available in many countries, offer opportunities for anonymous communication. If the mobile phones are purchased for cash at randomly selected retail locations such as convenience and discount stores, there is no linkage to the user and calls made on phones with preloaded minutes cannot be traced. If the phone is discarded after one-time use, any link with the user is destroyed.
Prepaid phone cards, first introduced in the United States in the early 1980s, have grown in popularity as a cost-saving convenience for students, travelers, and spies. Telecard companies began to flourish after telephone company deregulation, when advances in satellite and communications technology created excess system capacities. Rather than allowing their global telecom systems to remain idle, the large carriers sold hundreds of millions of minutes of system usage to Telecard companies for fractions of a cent per minute. Telecard companies resell these minutes (priced at pennies a minute) on phone cards at gas stations, airports, convenience stores, and chain stores in countries around the globe. Each prepaid phone card contains a concealed PIN number and allows the user to call at no additional charge to numbers within authorized countries up to the amount of minutes designated on the card.26
Phone cards provide travelers with an inexpensive means of calling home, but for illicit romances, criminals, and spies they eliminate records of the calls and provide complete anonymity. If a phone card is purchased for cash at a location not under the control of the host counterintelligence service, any call made using the card is anonymous and untraceable.27
Cuban agent Ana Belen Montes used phone cards and digital pagers as part of a covcom system for contact with her handler at the Cuban Mission to the United Nations in New York. To contact Montes, the handler would go to a remote public pay phone in New York City and use a prepaid phone card to dial the number of a digital pager she carried and transmit his message using a three-digit number code. Montes had also been instructed to anonymously purchase a prepaid phone card and proceed to a remote public pay phone in Washington, D.C. She was to enter the phone card’s 800 number, touch-tone the card’s unique PIN number, and dial a telephone number linked to a digital pager carried by the Cuban intelligence officer posing as a diplomat at the United Nations. With the connection made, Montes would enter a three-digit code to communicate secretly with her handler. Though the CuIS system provided anonymity to the users and the calls were un-traceable, her pattern of activity was alerting to FBI surveillance after she came under suspicion. Montes was known to carry a mobile phone, so there was no legitimate reason for her to seek out a remote pay phone to make a call after receiving a pager message. In this instance the covcom system was technically successful, but failed to mask the existence of the communication to well-trained counterintelligence officers.
Advancements in personal digital assistants (PDAs) in the late 1990s made it easier for information to be transmitted using SRAC techniques. FBI Special Agent Robert Hanssen, who “retired” from his role as a Russian spy when the Soviet Union collapsed in 1991, reactivated himself in 1999 and wanted to incorporate the latest digital technology for his secret communications. In a message to his handlers dated June 8, 2000, Hanssen wrote:
One of the commercial products currently available is the Palm VII organizer. I have a Palm III, which is actually a fairly capable computer. The VII version comes with wireless Internet capability built in. It can allow the rapid transmission of encrypted messages, which if used on an infrequent basis, could be quite effective in preventing confusions if the existence of the accounts could be appropriately hidden as well as the existence of the devices themselves. Such a device might even serve for rapid transmittal of substantial material in digital form.28
Advances in microelectronics and personal computers added to the capabilities and effectiveness of constantly improving covcom systems. Former MI6 officer Richard Tomlinson described a system known as “Garfield the Cat” issued only to long-term and highly trusted British agents in countries such as Russia and South Africa:
The agent writes a message on a laptop computer, then downloads it into the SRAC transmitter, a small box about the size of a cigarette pack. The receiver is usually mounted in the British Embassy and continually sends out a low-power interrogation signal. When the agent is close enough, in his car or on foot, his transmitter is triggered and sends the message in a high-speed burst of VHF. The transmitter is disguised as an innocent object. For many years “Garfield” stuffed animals were popular, as their suction feet allowed the agent to stick the transmitter on the side window of his car, giving an extra car signal as he drove past the embassy.29
In 2006, a spokesman for Russia’s Federal Counterintelligence Service announced on Moscow television that British diplomats had been photographed servicing an “electronic dead-letter box” hidden inside a fake, hollowed-out rock in a city park. A hidden video camera planted by the FSB photographed two men identified as British diplomats as they attempted to activate their nonworking “rock.” Concealed inside the rock were a receiver, transmitter, computer, and power supply designed for secret communication with a Russian agent. To activate it, the agent would secretly input his reports using only the keypad of a standard cell phone or other personal electronic device. Once prepared, the PED was placed in a transmit mode by using a combination of key strokes known only to the agent. The PED would then continuously send out a low-power signal, similar to Bluetooth technology, until it was within the range of the rock. Then, without requiring any additional actions by the agent who was carrying the PED concealed inside his coat pocket, the device would receive a confirming signal from the rock and transmit its encrypted information in a quick burst of energy. If the rock contained any stored messages for the agent, they would automatically be transmitted to his concealed PED.
The clever device updated the SRAC technology developed by OTS more than a quarter century earlier and made it safer. The agent’s PED appeared unaltered apart from an undetectable software modification. Even the low-power transmission to and from the PED had a range of only thirty feet, which made it difficult to detect. The agent’s handlers transmitted and received stored messages from the rock in a manner identical to that used by the agent. Once the rock had been discovered by the FSB, it was intentionally disabled to lure its caretakers, in this instance MI6 officers posted to Moscow as embassy staff members, to the rock to make repairs. The FSB announced that following the discovery of the first rock they also found a second rock concealed in a mound of snow at another location.30
Whether using OWVL radio in World War II, scrambled SRAC during the Cold War, or Internet steganography for the war against terrorism, every clandestine covcom system must meet five objectives:
• Break the transaction so if one end of the communication is discovered, it should not provide a link to compromise the person at the other end. The message content is secondary to the security of the agent.
• Use the best available physical or electronic hiding techniques. Covcom must always incorporate the most advanced technologies available at the time. Once a covcom system has been identified, the vulnerability of other agents being operated by the same intelligence service increases. The 1996 covcom techniques employed by Cuban agent Gerardo Hernandez and his Miami-based “Wasp” network proved helpful in recognizing similar tradecraft employed by Ana Belen Montes in 2001.31
• Employ strong encryption and ciphers to make the message so difficult to crack that, even if discovered, its contents are protected.
• Remain portable with capability to communicate with a variety of hardware platforms.
• Be backwards- and forwards-compatible, with sufficient flexibility to allow future security improvements to be incorporated while still allowing older communications to be read.
Jim Gosler concludes his essay “The Digital Dimension” in Transforming U.S. Intelligence with words of reality, caution, and optimism.32 In Gosler’s view, the reality facing the CIA is that intelligence services—allies and adversaries alike—have incorporated the “digital dimension” into their offensive and defensive operations. The caution for CIA operations is that defending against the sophisticated use of digital technology presents previously unknown and unaddressed gaps in its capabilities. The optimism is that twenty-first-century human and technical operations, when linked and mutually supportive, will solve problems otherwise intractable in either domain. A basis for such optimism can be seen in the history of OTS. The future effectiveness of American intelligence will depend on how well the lessons of that history are applied.