CHAPTER 11
Secret intelligence has never been for the fainthearted.
—Richard Helms, A Look over My Shoulder
Running concurrently with the Tolkachev operation, a parallel technical collection operation known as CKTAW remained one of America’s best-kept secrets.1 Generating new insights into Soviet particle beam and laser weapons research, CKTAW’s priceless intelligence did not come from an agent photocopying secret documents and loading dead drops in out-of-the-way locations. Neither did it arrive from the Big Technology of satellites with high-powered lenses. However, before it was over, the full spectrum of intelligence tradecraft and technology would come into play, from an orbiting satellite to hard won covert experience acquired over nearly a decade of successful operations handling agents in Moscow.
CKTAW was a wiretap on underground communications lines that linked the Krasnaya Pakhra Nuclear Weapons Research Institute in the closed city of Troitsk to the Soviet Ministry of Defense in Moscow.2 Data flowing via phone, fax, and teletype between the two facilities was recorded as it passed through a seemingly secure section of cable running beneath the streets of a Moscow suburb.
Tunnels and tapped communications lines had been previously used against the Soviets. The Berlin tunnel operation (Operation GOLD) in 1955-563 was conceived at a time when Soviet communications were mostly unencrypted and carried by underground telephone and telegraph wires. However, unprotected hardwired communications had fallen out of favor during the 1960s when governments and military commands adopted microwave links to communicate. These directional signals, transmitted from antenna to antenna in line-of-sight of each other, offered some security advantages. Though the towers were often visible, the directional transmission cone of the signals made them difficult to intercept without positioning an antenna between two towers, an espionage act that would have been impossible in Moscow.
In the mid-1970s, officers monitoring the RF (radio frequency) spectrum in Moscow discovered mysterious microwave signals with no clearly discernible origin. Eventually identified as data from a link connecting the MOD headquarters to the Krasnaya Pakhra lab,4 the signals unexpectedly appeared during rainstorms and suddenly vanished when the rain stopped.5 Engineers studying the phenomenon concluded that the temporarily exposed signals were caused by an atmospheric anomaly combined with one of the city’s unique architectural features. Apparently, the rain caused enough diffraction to send the secret microwaves ricocheting off Moscow’s tin-roofed buildings. The combination of rain and century-old roofs essentially turned a precisely targeted transmission into something resembling a broadcast. Rain and tuning to the right frequencies were all that was needed to listen in on some of the Soviet Union’s most closely guarded weapons development secrets.
The intelligence windfall was short-lived. When the Soviets became aware their microwave transmissions were vulnerable to intercept, both from land-based and satellite collectors, the signals diminished and then, eventually, disappeared completely.
U.S. analysts were certain that another, more secure communications link had been established, but did not know where it was located. Eventually, analysis of images from the new KH-11 satellite revealed that the Soviet military was laying communications cables in a trench running between Moscow and Troitsk.6 Launched in December 1976, the KH-11, the first space-based platform to use digital technology and transmit near-real-time images, provided eye-in-the-sky images from Moscow whenever it was in position and clouds did not obscure the target.7Corroboration of the image analysis came when CIA technical and operations officers in Moscow exploited information from every possible human and technical source to confirm that the trench did in fact carry the new Krasnaya Pakhra signals.
Closer examination of the route showed a series of manholes along the length of the buried communications link. The manholes were installed for routine repairs and security checks, but if the CIA could obtain access to the cabling from one of the manholes, perhaps the link could be compromised.
The job of identifying the best potential access point fell to CIA field officers who studied more than a dozen manholes along Varshavskoye Shosse (Warsaw Boulevard), a busy thoroughfare near Moscow’s outer ring road. However, like all Moscow operations, any actions to survey the manholes required exacting planning. How many times could Americans travel to the target locations without alerting the KGB surveillance teams? Could clandestine photography of the sites be acquired? How closely could a manhole be examined without attracting attention?
In the final determination only a handful of ground reconnaissance and casing trips were authorized. Each trip—either on foot or by car—required detailed planning, disciplined tradecraft, and, perhaps most important, timing calculated to avert suspicion. For an American to drive along a particular stretch of road outside his normal pattern of travel five times in a week was certain to tip off the ubiquitous KGB watchers that something about the area was of interest to the CIA. The few authorized casing runs required the participants to create new patterns of travel and eventually took more than two years to complete.
The essential casing photography was acquired with OTS concealed Tessina cameras. With high-altitude images, casing photos, and sketches, the Moscow office worked up a three-dimensional view of the CKTAW target site, including close-ups of notable features. Target sites along the heavily trafficked Varshavskoye Shosse were narrowed down as one target manhole after another was rejected. The specific manhole eventually selected for an entry point was in the worst possible location, except for the fact it was better than all the others.
The area along the narrow treeline that bordered Varshavskoye Shosse became one of the most carefully plotted and studied pieces of real estate on the planet. Details of the manhole, located just off the roadway, were painstakingly examined. Among potential problems were the worrisome 120-acre open field opposite the target, and a hostile installation belonging to the Second Chief Directorate visible on a hill two kilometers away. One positive feature was the treeline that ran parallel to the roadway. Although less than fifty feet wide, its foliage offered good ground cover for approaching the manhole from May through October.
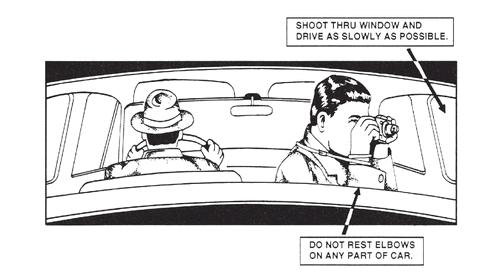
Depiction of proper technique for successful clandestine photography from inside a moving automobile, 1960. OTS continually improved spy cameras, but the techniques for taking quality photos remained unchanged.
Over several months, CIA officers covertly examined, photographed, and briefly entered the manhole. These operations allowed them to gauge the difficulty of removing its cover, measure the dimensions of the underground chamber, the depth of the ground water at the bottom, and confirm that the communications cables were accessible from a small steel utility ladder set permanently into one wall. The Soviets had not only shielded the cables in lead, but also installed sensors and alarms to detect any tampering. To tap a cable clandestinely meant not touching the actual transmission wires or compromising the integrity of the lead sheath encasing them.
Tapping the cable was a daunting challenge. So important was the potential intelligence carried over the line that in 1977, the CIA authorized an unprecedented, technically high-risk, and costly development program to do just that.
Technical expertise required coordination among multiple engineers to design and build the equipment and an interface among the developers and operations officers who would install and service the equipment. The operation included several DDS&T offices, a DO Division, and the National Security Agency. Management of CKTAW’s technical development resided with the DDS&T’s Office of Development and Engineering (ODE), the office responsible for satellites and other advanced technical sensor programs. The development team included several OTS engineers, with the operation eventually encompassing the Office of SIGINT Operations, the National Photographic Interpretation Center, and the DO’s Soviet/East European Division.
The system’s key component was a collar that surrounded the lead-sheathed cable and extracted the selected signals for capture by high-volume recorders at the site. The recorded signals were retrieved and returned to Langley where sophisticated equipment deciphered and analyzed the electronic pulses.
With the key technology still in development, the buzz of covert activity surrounding the target manhole continued. Memos, cable traffic, thick sheaves of casing photos, satellite images, operational proposals, and surveillance reports bounced between Langley and Moscow with particularly sensitive documents hand-carried by couriers. Refining the operational details required hours of discussions in the conference rooms at Headquarters and among case officers in Moscow.8
Over the course of the operation CIA officers would make periodic clandestine entries into the manhole in preparation for the installation of the collar and recording device. Officers trained for these assignments in a full-sized replica of the underground chamber at the CIA’s covert facility called “The Farm.” Rigorous sessions familiarized the officers with the operation’s physical demands, allowed them to practice the tasks to be performed in Moscow, and assessed their capability for carrying out the assignment. 9
Ken Seacrest was one of the OTS techs selected to enter the underground chamber. He would conduct a data sampling survey of individual communications cables to determine the one of greatest value. This critical phase of the operation would require Ken to remain alone, inside the manhole for up to two heart-pounding hours.10
The timing for an entry into the manhole was planned when Ken’s activity was least likely to be observed by a passerby on foot, in a passing car, or on a streetcar. Current schedules and routes of the Metro, trolley buses, and the electrichka were collected and studied along with the sometimes wildly inaccurate official and unofficial maps of the area. The mileage to the target area from the office and potential drop-off points were precisely measured, as were the exact distances and drive times during different times of the day.
To ensure he did not raise suspicion when approaching the manhole, Ken would disguise himself as an ordinary Muscovite. However, given the dated style of fashion available in Moscow, an American purchasing new local clothing would attract suspicion and shopping for used clothing would have been even more alerting to the watchers. So, Eastern European apparel of the right size, style, and matched to the season, was purchased at flea markets and thrift shops in Vienna, East Germany, and Warsaw. The clothing was carefully inspected, cataloged, and packaged at Langley before shipment to Moscow, where it was stored in a secure area to preclude potential KGB attempts to tag and track the items.11
Ken arrived in the USSR in the summer of 1979, after completing a six-month crash course in Russian.12 Among his fellow trainees was the senior operations officer slated to become CIA chief of Moscow. As part of his cover, Ken took an immediate interest in cultural activities of Moscow, never missed an opportunity to volunteer to show a visitor around the city, and spent as much free time as possible outdoors with his family. He filled their schedule with visits to tourist sites, cross-country skiing, and hiking. In short, he acted nothing like the intelligence officers depicted in the movies. Never an international man of mystery surrounded with beautiful women nor the toast of Moscow’s small American community, Ken did not own a James Bond tuxedo. His car of choice was not an exotic Aston Martin, but a sensible Volkswagen bus. He rarely used his newly acquired Russian language, since Americans who spoke Russian came under closer scrutiny. Ken appeared to be the dedicated family man with a moderate taste for culture and a love of the outdoors, who enjoyed playing broomball during winter’s short daylight hours and throwing darts in the evening.
In reality, Ken’s carefully selected cultural excursions and interest in the outdoors worked toward a single purpose—to build a persona that established a predictable pattern of activity that began on the day he arrived and would continue until he departed. As artfully engineered as a piece of spy gear, Ken’s job, hobbies, and interests—all of those elements that make up daily life—were meticulously designed before he stepped off the plane at Moscow’s Sheremetyevo Airport.
Like all other Americans in Moscow, Ken would be a potential target for surveillance and subject to assessment by the KGB. He would be closely monitored during his first weeks in Moscow for inconsistencies in the carefully crafted profile. It would not take much to catch KGB attention. One or two anomalies outside the normal pattern of activity would label Ken an intelligence officer, bringing continuous surveillance and compromising his operational value.
Within a few weeks Ken concluded that he fell into the KGB’s middle tier of surveillance priorities—an American who would be accorded periodic surveillance at random intervals. Even this would most likely lessen over time as surveillance observed him maintaining a consistent profile and pattern of activity in Moscow.
One critical piece of Ken’s activity was frequent family outings doubling as well-planned surveillance detection routes (SDRs).13 Whenever possible, Ken, accompanied by his wife and two small children, visited Moscow’s leso parks or “forest parks” on day trips. Large expanses of green—sometimes spanning hundreds of acres—these parks were a welcoming world away from the gray, soot-covered streets of Moscow’s center and a logical destination for a young American family that loved the outdoors.
Ken and his wife, Sharon, spent hours in the parks with their children, who were four and seven at the time, picnicking, throwing Frisbees, and hiking the long trails through the forests. The rucksack Ken carried became a familiar accessory to those who might have him under surveillance. The rucksack contained food, water, toys, and blankets for a day in the park. These excursions also provided a logical reason to visit all areas of Moscow, allowing Ken to familiarize himself with the roads, geography, and traffic patterns as well as identify choke points, escape routes, and observation stops for planning future SDRs.14 On days when they happened to have surveillance, Ken, with Sharon’s help, could practice identifying KGB vehicles, license numbers, surveillance tactics, and team members.
On a spring morning in 1981, five years of operational planning, targeting analysis, satellite imaging, signals intelligence, and technical development culminated in one of history’s most elaborately planned and expensive family picnics. Leaving home in the family’s green and tan VW bus, Ken began a twenty-mile trip that appeared identical to his past travel patterns. But in this instance, each road, each turn, and each stop was designed to detect and identify surveillance.
In their ears, Ken and his wife wore small radio receivers for the OTS monitors secured in harnesses near their armpits and tuned to the KGB’s 103.25 MHz primary surveillance frequency. Ken also carried a second receiver, a six-channel scanner that searched for any “near field” transmissions from militiamen and the ubiquitous Seventh Directorate.15
The inductive antennas looped around their necks were encased in soft fabric, concealed under their clothing, and transmitted the signals from the receivers to the earpieces no larger than the head of a Q-Tip. The small earpieces were concealed by latex sculpted by OTS disguise specialists to match natural ear contours and colored to blend with Ken’s and Sharon’s individual skin tone.
Each listened for the distinctive Russian word dvahd-tsaht awdeen (twenty-one), which translated from KGB surveillance code meant, “I have the target in sight.” If neither spoken numbers nor a series of clicks16 were heard, Ken could conclude with some confidence that surveillance was ignoring him that day.17
As the family drove toward the park, no words were exchanged about how Ken would spend the majority of the day or the possibility of surveillance. “We wouldn’t say much, particularly with kids there,” Ken explained later, “because at those ages you never know what they’re going to repeat or to whom. So they had to be totally unwitting about was going on.”
Ken initiated a series of maneuvers designed to detect surveillance. Unlike action adventure movies, where the hero eludes surveillance through a series of spectacular high-speed stunts, the reality of espionage for Ken was both more complex and prosaic. He did not zoom through intersections or make dangerous last-second turns to lose the followers. His driving had to fit the profile of a family man taking his kids in a van to a picnic. To any surveillance team that might have been watching, Ken took a more or less direct route to the park with all the speed his four-cylinder family van could muster.
Once he abruptly pulled off the road, grabbed a kid out of the backseat, and rushed into the treeline for an emergency potty break. He also missed a turn-off and circled back to get on the right road. There was also the need to study the map when momentarily lost. If a surveillance team had been following as he performed these common maneuvers, they could not have stopped without drawing Ken’s or Sharon’s attention.
The surveillance teams of the KGB’s Seventh Directorate were known to drive distinctive cars, usually the larger Volga, which resembled a mid-sized Volvo or the more compact Zhiguli, the Soviet version of a Fiat 124. Because only the KGB had automatic car wash equipment, their cars tended to be clean compared to other vehicles on the Moscow streets. Further, they boasted the luxury of windshield wipers, a valued commodity among those Muscovites lucky enough to own a car and often stolen if the car was parked unattended.
The SDR continued for more than an hour with Ken using a variety of seemingly routine stops and turns to confirm any vehicular surveillance.
Finally confident they were not being followed, Ken turned into a parking lot at the perimeter of the large park and pulled into a spot selected far in advance for the day’s picnic. Ken purposefully avoided the section of the park popular among Americans, where KGB teams might already be watching other targets. If he was not being watched, he wanted to avoid walking into active surveillance of another target. The family walked a couple hundred meters into the park before Sharon spread out their blankets on the edge of a grove of trees. Ken and Sharon continued looking and listening for surveillance as he began a series of apparently innocent explorations into the woods. Like the vehicular maneuvers, these were also intended to force any watchers to betray their presence.
After half an hour trying to enjoy the picnic lunch with his family and becoming reasonably certain surveillance was not nearby, Ken put on his well-used and stuffed rucksack, nodded to Sharon, and slipped into the woods. The wordless gesture told her that if he did not return by a certain time, she should load the children into the van and drive directly home. Using a prearranged signal, she would alert the chief that Ken had not returned as scheduled and was likely in some kind of trouble. The chief would immediately take action to minimize potential collateral damage to other operations and prepare the U.S. ambassador for the inevitable diplomatic blowback from the Soviet press announcing, “another American spy had been caught attempting to destroy the peaceful relations between America and the Soviet Union.”
As soon as Ken left the family, he began an extended surveillance detection run. There was need to reassure himself that he was clean before changing to Russian clothing.18 As he well knew, the Seventh Directorate did not always detain or arrest suspected intelligence officers during an operation, but rather continued to observe in the hopes of being led to an agent or dead drop site. Even then, the officer was often allowed to continue on his way as if nothing was amiss.19
That had happened to Penkovsky in late 1961. The Seventh Directorate watchers first spotted a man suspected of passing material to Janet Chisholm, wife of MI6 officer Roderick Chisholm, inside a doorway just off one of Moscow’s busy shopping streets. Rather than make an arrest, they increased surveillance and eventually spotted the same man a few days later in a public park making another exchange. The unidentified subject was then placed under surveillance and later identified as GRU Colonel Oleg Penkovsky.
The spy, not the intelligence officer, was the ultimate target.20 However, once the KGB had identified an agent, arresting the foreign intelligence officer during an operation offered additional value. When the KGB arrested Martha Peterson on the Krasnokaluzhsky Bridge in 1977, although TRIGON was probably already dead, her detention brought negative international publicity to the United States and disrupted CIA operations in the USSR.
As Ken walked the paths of the park, the decision of whether to go to the manhole site was complicated by the number of people around him. Soviet citizens frequently used Moscow parks and on this early spring day, with the snow off the ground and the weather warming, the park was particularly crowded. Ken knew crowds could be used to his advantage, allowing him to blend into packs of visitors, but they also served a similar function for KGB watchers.
There was also danger in looking too closely at every person that crossed his way. Training and experience had taught Moscow personnel that if they looked hard enough, anyone could seem out of place. Since surveillance teams attempted to imitate everyday life, ordinary citizens can easily be mistaken for more than they really were. The old man wearing a cloth cap and walking slowly with a cane, the young couple strolling hand in hand along a path, a mother with children seeking a few hours’ reprieve from a small apartment, or the stout, middle-aged lady with the ubiquitous plastic “perhaps bag” swinging at her side—any one of them could be members of the Seventh Directorate.21 Then again, they could be just what they appeared to be, Muscovites enjoying a spring day outdoors.
Ken was well aware of this particular operational paralysis. Intelligence officers called it “seeing ghosts.” The psychology of the phenomenon was rooted in the inherent anxieties of clandestine activity coupled with the real possibility of encountering hostile security. What made it particularly vexing was the uncertainty of proving a negative. If one observed surveillance, or heard transmissions over the monitor, it became a certainty, but if one did not see or hear surveillance, several possibilities came into play. There could be no surveillance, the officer had not identified surveillance, or surveillance could know where he was headed and be waiting there.
To combat the uncertainties, Ken relied on confidence that previously effective SDR techniques would work again. In the end, it came down to trusting experience, training, and whatever technology was at hand. When well executed, the plans, maneuvers, and detailed routes that had been so carefully constructed, studied, and practiced should reveal surveillance, but ultimately Ken would act on his instincts. Even if his elaborate vehicular and foot SDRs did not reveal surveillance, Ken, like every other officer, had the option to abort the operation based on nothing more than “gut feeling.”
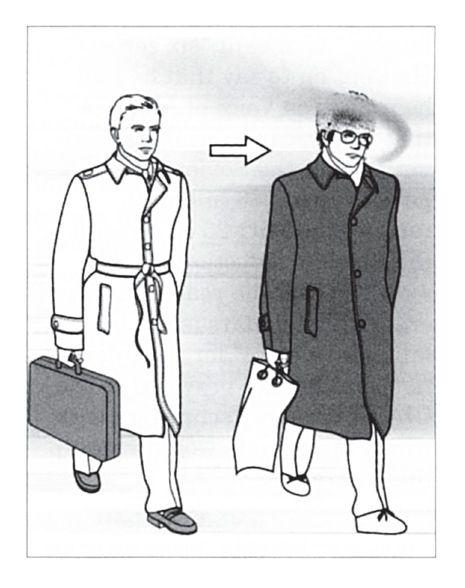
Case officers frequently donned light disguises, such as that of a Russian worker, for meeting with agents in Moscow, circa 1982.
“You absolutely trusted the process. But at the same time, you developed an intuition about what was there and what wasn’t,” Ken explained. “After a while you began to get a feel for these things. Something might just not feel right.”22
So, despite all the planning and preparation that came before, the final decision of “go, no go” was Ken’s alone. With the park goers bustling around him, he paused, took several deep breaths of the chilly spring air, and decided, “It’s a go.” Entering an isolated section of forest, he quickly changed from his American clothes into the local clothing stuffed in the backpack.
The Russian clothing offered a fair degree of camouflage by blending in among the other drably dressed Soviet citizenry. Soviet clothing, in 1981, had little of the style found in Western fashions. The outfit Ken now sported featured well-worn grays and browns, a brimmed fedora-like hat, inexpensive Russian shoes, a knee-length overcoat, and rough, ill-fitting trousers. He would not have looked out of place in a World War II film among the costumed extras who populated the set of a crowded train station.
Casually draped on one shoulder was the rucksack with its unusual “picnic” supplies. Weighing nearly thirty-five pounds, it contained, along with his original clothing, a twenty-million-dollar investment in advanced U.S. eavesdropping equipment designed to extract and record signals from lead-sheathed communications cables the Soviets considered tamperproof. If discovered by the KGB, not only would the mission aimed at critical intelligence abruptly end, a technical collection capability that could be applied to similar targets in other parts of the world would be exposed.
Walking through the groves of birch that bordered the park, Ken took a lengthy, circuitous route leading him out of the park and immersing him in Moscow’s general population on the public transportation system. Changing buses several times, his face set impassively, Ken became indistinguishable from the other passengers. The trolleys and buses made their way through Moscow traffic, carrying him far from the manhole on Varshavskoye Shosse and then, eventually, returning him to within walking distance of the target.
At each change of bus and trolley, Ken tried to be the last to step off and observe if anyone else was rushing to get through the closing doors. Still wearing the receivers, he listened for surveillance transmissions corresponding to his actions. Like the vehicular SDR, some elements of Ken’s foot SDR were designed to compel improvisation by his KGB watchers, forcing them into the open by making mistakes. Other elements of the routine allowed him to pick out patterns or repetitions in surrounding faces. Was the young couple he noticed earlier in the park now getting on a bus far from where he first spotted them? Was it the same girl, only now dressed in a different coat and hat? Was the license plate of the car that trailed a respectable distance behind the bus the same one he had seen a half hour earlier?
Ken followed the procedures, moving steadily toward the time when he would make the second crucial decision: entering the manhole. The right choice meant the beginning of an operation that pried open the door to a potential treasure of intelligence. The wrong decision would result in his arrest, identification as a CIA officer, expulsion from the USSR, and collapse of a multimillion-dollar operation that had the attention of the highest levels of the U.S. government.
Exiting the bus at the final stop of his journey, Ken hiked three kilometers to the site. Although he had never been this close to the target before, the maps, casing photos, and satellite images that he had studied for months gave the surroundings a sense of familiarity. The site was “as advertised”— technically promising and operationally vulnerable. Partially obscured by the narrow treeline, the new spring’s foliage offered marginal cover. A curious look in Ken’s direction at the wrong time from the driver of the tractor working the nearby field or the unexpected presence of a Soviet citizen who had wandered off the beaten track in search of wild mushrooms—any of these or a thousand other unforeseen pieces of ordinary bad luck could wipe out years of planning and research.
The leafy trees along the roadway shielded Ken as he slipped into a pair of chest waders and pulled a specially made tool from the backpack to open the manhole. The operation required simple, as well as sophisticated technology. Once in the manhole, the waders would provide warmth and dryness. But first, the manhole’s heavy metal cover had to be removed quickly, a task for which OTS had designed a special implement. Fashioned from aluminum, the 12-inch curved tool was compact and lightweight, but strong enough to lock into a utility hole and pry the heavy iron slab from its position.
Moving to the manhole, Ken inserted the pry bar and lifted, sliding the cover off the hole just enough to lower himself into the dank semidarkness. “That was easy,” he thought, and made a mental note to thank the designers of the pry bar when he was back at the OTS lab.
Descending the ladder, Ken stepped into cold water. Looking up through the partly opened manhole, he could see only a small slice of gray sky and a thick cluster of treetops. Measuring four feet by six feet, the chamber was eight feet from bottom to top. Exiting from a matrix of conduits on one side of the manhole and reentering an identical conduit matrix on the opposite side were the lead-shielded cables that carried the target communications along with the rubber-encased civilian telephone lines.
Thigh-deep in cold water, Ken began the technical part of his clandestine work. His objective was to obtain samples of communications from the streams of high-speed data traffic flowing through the dozens of wires contained in each of the lead-sheathed cables. Although the CIA was confident that Krasnaya Pakhra communications were carried in one or more of the cables, Ken needed to identify the specific cable of primary interest by sampling signals from each of the dozen cables.
The sampling and monitoring device carried in the shabby backpack was engineered to pinpoint that cable. Designed by a private CIA contractor, the collection equipment had been shrunk down into a 25-pound package that looked like a rectangular portable radio with an array of indicator lights mounted on the top and leads set into one side to accommodate several probes simultaneously. The extracted data was recorded on what appeared to be a standard cassette tape, though capable of capturing high-quality signals on multiple tracks.
Pulling the device and various components from his backpack, he meticulously assembled the equipment before applying a probe to the first cable. The only indication of technical success for Ken, standing in the bottom of the manhole, would be if the tape moved and the light came on. If an indicator light failed or the tape malfunctioned, he had no way to troubleshoot the system and would need to abort the operation.
Ken placed the formfitting two-piece sensor, one section at a time, on either side of a cable and strapped it together with lengths of white fabric measuring a foot long by an inch wide. He then tightened and buckled the strap to hold the sensor in place. Ken’s twelve buckling straps were white by design. If he dropped one, white would be easier to spot in the poorly lit manhole. Twelve was also an easy number to remember when he inventoried the gear prior to leaving the hole. No evidence of an unauthorized entry could be left behind.
A grid of more than a dozen underground cables entered the chamber, although Ken’s attention focused on the well-protected, lead-sheathed, and gas-filled cables whose very design betrayed their significance.23 Since the data flow was often irregular, he needed to keep the monitors on each cable long enough to get an adequate sample.
Above, the noise of traffic whizzing by only a few yards away was a constant reminder of Ken’s vulnerability. If an inquisitive Soviet citizen crossed the road to look down the partially uncovered manhole, he would have come face to face with a CIA officer standing in ground water amid a thick cluster of cables.
It was tedious work. The position of each conduit and cable needed to be identified in a logical way. Working from a checklist, Ken collected samples, made identifying notations and then moved on to the next grouping. A small “bookkeeping” mistake of misidentifying a single cable could invalidate the sampling. Working methodically, he was conscious that each additional minute in the hole increased the chances of discovery, while haste could lead to unacceptable mistakes.
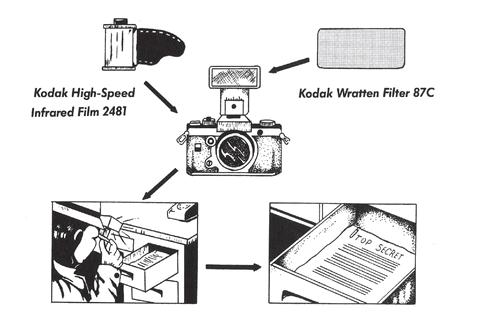
Infrared film combined with a Kodak Wratten 87C filter covering the flash allowed undetectable photography of documents or objects under low-light and dark conditions.
Ken had a second mission, as well. While waiting for sample collection, he “cased” the chamber, photographing the conduit and cable layout using a 35mm camera outfitted with an infrared flash unit.24 This documentation would provide a current and complete record of the underground chamber, including details that could assist in any final design changes of the collar for permanent installation.
Finally satisfied that he had collected and recorded adequate samples of the data, Ken inventoried his tools, repacked the equipment, climbed up the ladder, and poked his head out. With no one in sight, he emerged from the manhole, quickly slid the heavy cover back into place, and retreated toward the narrow treeline where he removed the waders and stuffed them back into the rucksack.
Ken was some distance from his family but the preplanned route that returned him to the picnic area was more direct than the one that brought him to the target. After walking into the park with no evidence of surveillance, he found another secluded spot, changed out of the street disguise, and returned to his wife and children looking the same as when he left a little more than five hours before.
Sharon, although relieved to see Ken, understood the operation was not yet a success. If surveillance had paid attention to her and the kids and noticed Ken’s absence, that would raise questions. American men did not normally leave their families alone in a park for hours on end.
Wasting no time, they gathered up the children along with the picnic gear and headed back to the VW bus. Neither Ken nor Sharon relaxed on the drive home with the invaluable tape and tapping equipment in their possession. They drove carefully and continued observing cars behind and in front of their van, since no American was immune from accidental or KGB-staged automobile mishaps that could result in questioning or search.
No celebration awaited Ken, although the chief anxiously anticipated a reason to return to his office that evening. While he had received no emergency signal from Sharon, he went to the office, opened the door, flipped on the light, and saw a sheet of paper torn from a government-issued notebook taped to the wall. Scrawled in pencil on the otherwise blank page was “#1.” It was Ken’s simple signal announcing the success of a critical phase in the CIA’s most advanced technical operation in the USSR.
Based on the analysis of Ken’s sampling, CIA identified the primary target cable and authorized installation of a permanent tap. For several years CKTAW successfully recorded communications between Krasnaya Pakhra and the Soviet Ministry of Defense. Then, in the spring of 1985, something went wrong. An officer sent to recover the tapes from the recording device aborted his mission when remote interrogation of the unit returned a “tamper indicated” signal.25 After a few weeks, a second trip to the site did recover the tapes, but the system had ceased functioning and the entire operation was shut down.26
What had gone wrong? For years, the virtually trouble-free American penetration of top secret Soviet data streams had gone undetected before suddenly coming to a halt. CIA counterintelligence officers speculated the reason behind CKTAW’s loss was more sinister than just simple “bad luck.”27 Had the KGB discovered the tap because of an error with a case officer’s tradecraft during infrequent trips to recover tapes? Could the KGB have a spy who was privy to one of the CIA’s most tightly held operations? As with the roll-up of an agent, the failure of the device left a host of questions, though for CIA counterintelligence the answers were not long in coming.
On August 1, 1985, Commander Vitaly Sergeyevich Yurchenko,28 deputy chief of the First Department of the KGB’s First Chief Directorate (foreign intelligence), called the U.S. Embassy in Rome and offered to defect.29 Later that afternoon Yurchenko provided the chief, Alan D. Wolfe, with information about two penetrations of U.S. intelligence, one at the National Security Agency and a second, code-named ROBERT, within the CIA itself. 30
Yurchenko claimed not to know ROBERT’s true name, but offered two important clues: ROBERT had sold classified information to the KGB in Vienna in the fall of 1984 and trained for Moscow operations, but was taken off the assignment just prior to departure.31 Two days after receiving Yurchenko’s information, the CIA’s Office of Security informed the FBI that ROBERT was almost certainly the former CIA officer Edward Lee Howard. 32
Howard, who joined the CIA in 1981,33 had been selected in 1982 to become a case officer in Moscow. Since he had always been under cover as a CIA employee and had not been posted abroad, he was considered clean and less likely be identified as an American intelligence officer.34 In preparation for the Moscow assignment, Howard and his wife, Mary, received six weeks of intensive training on the clandestine tradecraft necessary for operating against the KGB in their own backyard.35 Training in detecting and evading surveillance was particularly rigorous with field exercises conducted against FBI surveillance teams.36 Then, during a polygraph examination before his scheduled departure for Moscow, Howard admitted to drug and alcohol abuse, petty theft, and cheating during training.37 The CIA fired Howard in early May of 1983.38
Bitter and angry at the Agency, Howard moved to Santa Fe, New Mexico, where he took a job as an economic analyst with the state legislature. But his troubles with alcohol and debts continued.39 A series of bizarre telephone calls Howard made, including one to the U.S. Embassy in Moscow, were so troubling that on September 24, 1984, a former supervisor and a psychologist were dispatched to interview him at his home.40 Howard revealed the unsettling news that in October of 1983 he loitered outside the Soviet Consulate in Washington, D.C., while considering whether to volunteer to the Soviets.41
Following receipt on August 3, 1985, of the CIA information identifying Howard as ROBERT, the FBI began surveilling Howard, but by the end of the month, Howard, sensitized by his training, detected the surveillance.42 In early September the FBI began monitoring his telephone conversations.43 Howard was under twenty-four-hour physical and technical surveillance.44
A little more than two weeks later, on September 19, the FBI confronted Howard with information that he had been identified as a Soviet agent.45 To protect the real source, Yurchenko, the FBI attributed the information to KGB defector Oleg Gordievsky.46Howard did not confess, but refused a polygraph test.47 Interviewed again the next day, he stated his intent to engage a criminal attorney over the weekend and agreed to another interview on Monday, a meeting he never intended to attend.
During his CIA countersurveillance training, Howard had learned to use the JIB and how to roll out of a moving car while slowly rounding a corner. 48 Lacking an OTS-designed JIB, he created a field-expedient version with a toilet plunger, coat hanger, and Calvin Klein field jacket taped to the top. The dummy’s head was a Styrofoam wig block and commercially available Jerome Alexander wig issued during his disguise training at “The Farm.”49
Howard and his wife departed for dinner at a local Santa Fe restaurant on Saturday evening. While driving home they made a slow turn off Garcia Street onto Camino Corrales and Howard jumped from the car into the bushes.50 Mary propped up the makeshift JIB in the passenger’s seat, buckled it in place, and minutes later the FBI surveillance team clearly saw two “people” in Howard’s 1979 Oldsmobile as it entered their garage.51
After spending the night at an airport hotel, the next morning Howard was on the first available flight from Albuquerque to Tucson, where he continued his secret journey to Moscow.52 The FBI did not discover his escape until some twenty-five hours after he jumped from the car.53
Howard’s defection had a catastrophic impact on Moscow operations. His devastating betrayal exposed to the KGB collection systems, tradecraft techniques, covert equipment, and agent-handling methods inside the Soviet Union and specifically CKTAW.54Howard had been one of the handful of officers to participate in the CKTAW operation and, in fact, during the polygraph examination that led to his dismissal, admitted cheating during an exercise in the mock-up of the manhole by replacing the weights in his backpack with cardboard to make it easier to get into the small opening.55
Almost a year later, on August 7, 1986, TASS announced that Howard had been granted political asylum in the USSR.56 Reportedly, Howard continued drinking heavily and died at age fifty, in July 2002. Russian news reported the cause of death as a broken neck from a fall. Neither the Russian nor American intelligence services mourned his death.57
The significance of the American spy technology the KGB recovered from the manhole and the nearby cache was not lost on Soviet leadership. In a 1990 article that described and decried U.S. technical espionage against the Soviet Union, Lieutenant General Nikolai Brusnitsyn, deputy of the State Technical Commission of the USSR, complained that collection systems like CKTAW were interfering with arms control and reduction efforts between the two superpowers.58 Brusnitsyn concluded by admitting to Soviet “anxiety over the ever-growing capabilities and scope of intelligence gathering and spying technology.”59
Almost ten years later, in 1999, veteran KGB counterintelligence officer Rem Krassilnikov, author of The Phantoms of Tchaikovsky Street, provided a Soviet version of the CKTAW operation, which the KBG had code-named BILLIARD BALL.60 Krassilnikov described an “inductance data sensor” in the manhole as being connected to a metal box containing a tape recorder, control system to turn the recorder on and off during conversations, transceiver, and an internal power supply capable of operating the device for four to six months.61 According to Krassilnikov’s account, the box was buried a half meter deep and located not far from the manhole cover. In this KGB version, the box was painted bright red with the Cyrillic inscription DANGER! HIGH VOLTAGE, protected by rodent repellent, and connected to a nearby ultra-shortwave (UKV) antenna.
Krassilnikov, citing the KGB’s technical analysis, reported the transceiver could be remotely interrogated up to 2.5 kilometers away. It responded with a coded signal indicating whether the unit had been disturbed, needed to have its tape changed, or required a replacement power supply.62The analysis estimated that it was necessary for the CIA to service the unit only every four to six months.
CKTAW’s compromise did not diminish its achievement. For the CIA, the operation represented another remarkable fusion of technical reach and operational tradecraft, revealing vulnerabilities in the Soviet security apparatus. The imagination that conceived the operation, the engineering talent that built the system, and the operational execution represented a new kind of American technical collection capability. In the coming decades, the technologies developed during the CKTAW operation would be repeatedly applied to other equally critical targets.