SECTION IV

Crest of OTS audio operations officers, 1970s.
CHAPTER 12
If it ain’t audio, it ain’t shit.
—Unofficial motto of audio techs
They were called audio techs and for more than two decades—from the 1960s until the 1980s—they were at the top of an unofficial OTS caste system. Aggressively mounting hundreds of audio surveillance operations around the world, these few hundred officers worked on the frontline of Cold War espionage. Their missions took them from European capitals to the most remote destinations on the globe, responding to stations that saw an opportunity to “collect audio.”
Although CIA audio operations inside the borders of the primary Cold War “hard targets” (the USSR, China, Cuba, North Korea, and North Vietnam) were severely limited by internal security services, conditions in Europe and Third World countries were far different. In these countries, clandestine audio operations could be launched against the residential quarters, official buildings, and embassy compounds of the hard-target countries. This was particularly true in the Third World where security was often less stringent than in major European cities.
When operations levied a “requirement,” it was expected a tech would catch the next plane for Paris, Rome, West Berlin, or a Third World country in turmoil whose new name had yet to be printed on maps or the new leader’s visage on currency. The techs worked under aliases as businessmen, military personnel, or adventure-seeking vacationers, becoming whatever allowed them to blend in with other travelers and provided the most effective cover. A tech might get off a plane in a South Asian country, spend a week planting a bug, then fly home for the weekend, change identities, and find himself in Africa by Monday evening.
Their exploits and sophisticated gadgetry rivaled the popular fictions of globetrotting intelligence officers. OTS audio techs slipped into basements and sewers to tap phone and communication lines, moved silently over roof-tops, walked narrow beams through the crawl spaces of attics, and scaled the walls of fashionable villas in the dead of night. They were sent into diplomatic compounds, business offices, residences, hotel rooms, limousines, airplanes, and boats to plant audio devices. Accurate and sometimes embellished accounts of their operational adventures established what would become known as the tech culture, eventually defining, for better or for worse, all OTS techs regardless of their clandestine discipline. Among the most enduring of these professional and personal attributes was the techs’ seemingly unwavering fondness for cheap hotels and cold beer.1
There were practical reasons for what could be perceived as “less than sophisticated” tastes among these world travelers who commonly logged more than 100,000 air miles annually and were away from home 150 nights a year. Although government employees on official travel were not permitted to accumulate frequent flier miles, they were allowed to keep any funds left over from the daily government food and lodging allowance.2 The resourceful techs found they could supplement their modest salaries by staying at inexpensive hotels—a type of lodging that became known throughout the Agency as “tech hotels.”
More important, the techs’ choices when it came to accommodations and beverage made sound operational sense.3 Whereas case officers traveling abroad needed to match their selection of accommodations with their cover position and operational role, techs usually wanted to get in and out of town while keeping the lowest possible profile. As a rule, they maintained erratic schedules, working when the target was accessible, regardless of time, weather, or holidays. If that meant access to a consulate or embassy could be obtained only after it closed for business, then the tech’s workday would likely begin at nightfall and end before dawn. Whatever bargain lodgings may have lacked in comfort or basic amenities, such as heat, hot water, or a private bathroom, they made up for by way of discretion.
Luxury or business traveler hotels tended to boast large, attentive staffs that would notice an American businessman leaving late in the evening and returning in the early hours of the morning with traces of plaster dust on his shoes or paint flecks in his hair. On the other hand, tech hotel staff conveniently overlooked the comings and goings of their guests. If an American departed in the early evening and returned just before dawn with his hair matted with sweat and in need of a bath, it would not be the first time such a thing happened.
One technical operations officer realized he had ventured too far down the hostelry pecking order when the desk clerk asked incredulously, “You mean you want the room for the entire night?” Another tech found his own limits of frugality tested when he and his partner checked into a hotel offering a double bed for $3.50 a night. “You know, if we shared a room, we could cut the cost in half,” the aggressively thrifty tech suggested.
As for their reputed penchant for beer—well, beer just tasted good and made other deficiencies seem less important. It was also safe. In countries where drinking the local water was a health risk, beer served double duty as thirst-quenching beverage and “water” for brushing teeth. During one operation that confined six techs in a target facility for several days, the team member in charge of providing food provisioned generous quantities of beer, canned tuna—and nothing else. In the sweltering heat of the empty warehouse, the odor produced by a sustained diet of tuna and beer led to a unanimous vote to prohibit that particular tech from outfitting the team with provisions again. Ever.
Despite living and working in these austere conditions, techs brought “technical magic” to operations. Their sophisticated gear tapped into secrets hidden behind the high walls and closed doors of secure installations. Their equipment combined with expert installation captured the private conversations of people to whom the Agency had no other access. The moods, personal doubts, and aspirations of potential recruitment targets held on reels of audiotape offered case officers a unique peek into their professional and personal world. Recordings of official discussions of policy and diplomatic strategies provided CIA analysts and policy makers with well-sourced, hard strategic intelligence as well as tactical counterintelligence that supported law enforcement.
None of this was lost on the techs themselves—neither the excitement of the operations nor the value of the intelligence take. “If it ain’t audio, it ain’t shit,” became their unofficial motto and was proudly displayed on the desk of the audio chief during the 1970s. They were the “top guns” of the OTS and none of them doubted it for a second. However, the colorful tech culture, the technology, and the intelligence that flowed from it did not materialize overnight. The advanced technology, like the tech culture, evolved over two decades. The devices as well as the expertise to make them work were built from the ground up.
The Technical Services Staff was not a year old in 1952 when the CIA received information about an alarming audio discovery in Moscow. During an electronic sweep, the countermeasures team discovered a device secreted in the wooden replica of the Great Seal of the United States that hung behind Ambassador George Kennan’s desk in his residence at Spaso House, barely a mile from the Kremlin, at No. 10 Spasopeskovskaya Square.4 The seal had been hanging there seven years, after a group of Soviet Young Pioneers presented it as a token of friendship on July 4, 1945, to then U.S. Ambassador, W. Averell Harriman. The gift, presented by smiling children in neatly pressed uniforms, concealed a listening device that would baffle and frustrate the Agency for years. “The Englishmen will die of envy,” Valentin Berezhkov, Stalin’s personal translator, whispered to Ambassador Harriman during presentation.5
That the Soviets bugged the U.S. Ambassador’s office should have come as no surprise to anyone. When American diplomats first arrived in Moscow in 1934, they discovered that listening devices inside their offices and residences would be the way of life within the Soviet Union.6 U.S. Ambassador Llewellyn Thompson, posted to Moscow between 1957 and 1962, and again between 1966 and 1969, would walk in Red Square for private conversations. 7 As a young diplomat in the 1930s, Kennan personally played amateur spy hunter in Spaso House by hiding in the billiard room overnight—with a partner in the attic—in an unsophisticated attempt to catch the Soviet techs planting devices.8
Further evidence of the Soviet’s use of eavesdropping was demonstrated by the NKVD’s (forerunner to the KGB) aggressive operations during World War II. In the late fall of 1941, as German forces approached Moscow, the Soviet government ordered foreign diplomats out of the city to the relative safety of Kuybyshev (Samara). Then, with foreign embassies standing empty or hosting only skeleton staffs, the NKVD hardwired virtually every Western embassy in the city with embedded microphones. After the German army’s advance halted just twenty miles outside Moscow in early 1942, the diplomats were allowed to return to the Soviet capital and their bugged embassies.9
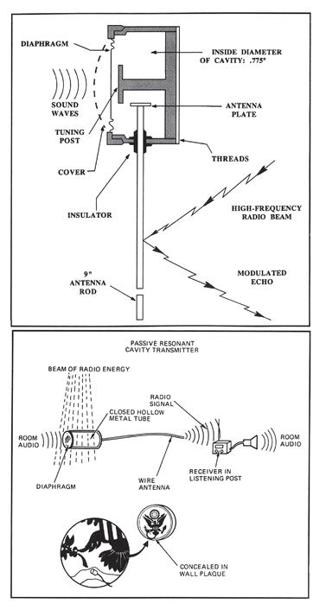
The bugged Great Seal of the United States that hung over the U.S. Ambassador’s desk in Moscow contained a passive cavity resonator and went undetected for seven years, from 1945 to 1952. The CIA had no comparable audio technology at the time.
The NKVD bugged the rooms and conversations of President Roosevelt and British Prime Minister Churchill during the Tehran and Yalta summit meetings.10 In Tehran, in 1943, Stalin maneuvered the American President into staying in the Russian compound amid rumors of a German assassination plot. At the 1945 Yalta conference, the NKVD techs employed an early version of a directional microphone to capture Roosevelt’s private outdoor conversations at a distance of fifty to one hundred meters.11 When Churchill’s daughter, Sarah, made an off-hand comment that lemons might be just the thing with caviar (in another version of the story Sarah suggested lemons with tea), a lemon tree reportedly appeared in the orchard overnight.
After receiving the audio take from these operations, Stalin pushed his intelligence service for more and more information, insisting they report even the tone of voice in transcripts. After devouring the raw intelligence delivered each morning with his breakfast, Stalin would then act taciturn, even bored, during the actual meetings.12
However, what was discovered hanging behind the Ambassador’s desk in 1952 was revolutionary in the technology of listening devices. Implanted in the middle of the carved wood of the Great Seal, cleverly hidden behind an air passage formed by the American eagle’s nostril, was a device that was alarming as much for the technology it employed as the fact it had been active for more than half a decade. Indeed, four American ambassadors—Averell Harriman, Walter Smith, Alan Kirk, and George Kennan—presumably had their secret conversations picked up by the bug.
Differing significantly in design and function from any piece of covert listening equipment previously known, the device was constructed of precision-tooled steel and comprised a long pencil-thin antenna with a short cylindrical top. Agency engineers could not understand exactly how it worked. The stand-alone unit, apparently, did not require a battery or any other visible power source. It had no wires or tubes, nothing that identified the device as a piece of electronic equipment. If the oddly shaped length of metal was transmitting conversations, then how was it doing it?
“The Thing,” as it was soon dubbed, bounced among the Agency’s lab, the FBI, and private contractors for evaluation and reverse engineering. No one could offer anything beyond an educated guess as to how The Thing worked, and somewhere in its travels from lab to lab it was damaged from either improper handling or shipping.13
The Thing was eventually sent to Peter Wright, the principal scientist for MI5, the British intelligence service responsible for counterintelligence operations. Wright worked for more than two months to solve the mystery before eventually coaxing it into operation. He dubbed it a “passive cavity resonator.”14 The Thing, as Wright discovered, worked by reflecting radio waves, then picking those echoes up with a radio receiver.
To operate the device, the NKVD aimed a continuous 800 MHz radio signal at the seal from a listening post in the building across from Spaso House.15 The Thing’s thin diaphragm at the top, which Wright had repaired, vibrated with the sound of a voice. Those vibrations were carried by an interior tuning post to the antenna. Then, as the vibrations hit the antenna, they altered the reflected radio signal that bounced back to the listening post.16 The Thing did not require internal power in the same way a mirror does not require power to reflect light. The radio transmitter and receiver, code named LOSS (or REINDEER by the Russian techs), were a marvel of signal processing, considering the technology available at the time.
According to Wright’s own account, once he understood the principle and made the device work, he took another eighteen months to create a similar system for British intelligence. Called Satyr, his device featured aerials—transmitter and receiver—disguised as two proper British umbrellas. 17 Satyr proved to be a great success and Wright called it “black magic.”18 Then, as he observed, “the Americans promptly ordered twelve sets and rather cheekily copied the drawings and made twenty more.”19 The American version of the device, according to Wright, was called Easy Chair (also Mark2 and Mark3).20
The concept behind The Thing represented a remarkable leap forward in eavesdropping technology. Viewed as a wake-up call at CIA for audio operations, it was the clandestine equivalent to Sputnik. The Agency had to play technological catch-up in RF audio as well as in space.
Ironically, although they did not know it at the time, many of the scientists who had worked and failed to decipher The Thing’s mystery would probably have recognized the name of its creator, Lev Sergeyevich Theremin. 21 A musical prodigy and physicist, Theremin was born in czarist Russia in the late 1800s, excelled at some of Russia’s finest universities, and his genius was recognized by the Soviet regime. He lived in New York City during the 1920s and 1930s where he demonstrated the electronic instrument that bore his name. The theremin was played without touching it and enjoyed a brief life as a serious instrument. In the 1930s it captured the imagination of the avant-garde of the jazz age, though eventually it was relegated to creating the spooky sounds heard in horror and science-fiction films.
Those who crowded ballrooms and concert halls to hear Theremin’s thoroughly modern instrument, or caught glimpses of him amid Manhattan’s high society, never suspected that the socially sophisticated “Russian genius” was also covertly working for Soviet intelligence. Just before the Soviet Union’s entry into World War II, Stalin summoned Theremin back to Moscow where he was summarily sent to a Siberian prison camp. Later he was transferred into one of the KGB’s secret laboratories—a sharashka—to work on creating spy gear. After developing The Thing,Theremin was awarded one of the Soviet Union’s highest honors, the Stalin Prize First Class, along with the equivalent of $20,000, a fortune in Soviet society, but remained imprisoned.22
At its formation in September of 1951, the CIA Technical Services Staff employed fewer than fifty people. Its scientists and engineers were housed in a makeshift lab at Indian Head, Maryland, thirty miles south of Washington, D.C. The facility, a one-time gun test facility for the Navy, sat on a large peninsula that jutted out into the Potomac.
“Somehow the Agency begged, borrowed or stole some space down there, but conditions were bad. We had to do our own janitorial service. We complained, but we did it,” remembered Kurt Beck, an engineer who worked in that first lab. “When we started, there were a dozen people overall and maybe six to eight people working in the audio program.”
The Thing arrived at the TSS lab in 1952, but the audio engineers had no point of reference against which to assess the device or understand how it worked. Data on covert listening and transmitting devices, comparable to research on military weapons systems or private sector consumer products, simply did not exist. Cataloging data on technical collection devices was a new concept for American intelligence and the Soviet passive resonator technology exceeded anything TSS could even attempt.
However, like all “finds” (discoveries of clandestine devices), The Thing revealed certain key capabilities of its host service.23 The first was the cleverness of design. The Thing demonstrated that Soviet intelligence possessed a technical expertise not matched by the CIA. Second, the construction suggested that the Soviet engineering approach relied on creating one-off custom-made pieces specifically produced for each operation. The device was not mass-produced or made in a serial production of fifty or a hundred identical units with interchangeable components. To the TSS engineers, The Thing looked to be expertly crafted and built entirely by hand.
The Thing underscored deficiencies in U.S. technical capabilities compared to the Soviets as well as highlighting some Soviet weak points, such as a lack of technical innovations spurred by a consumer-based economy. Without private industries to offset some of the costs of building laboratories or production facilities, the Soviets’ intelligence service had to underwrite all the costs for developing spy gear. This contrasted sharply to the OSS tradition of recruiting private industry to support intelligence. There could also be little doubt that The Thing was the product of Russia’s long involvement with espionage dating back to the time of the czars while America’s espionage capability, particularly in the technological sense, was still in its infancy.
The engineers at Indian Head recognized the huge gap as well as the larger, more basic and immediate question facing them: Precisely, how do you go about building a better bug?
The state of available technology in the 1950s limited the CIA’s audio operations to little more than running a microphone wire or a telephone line to a set of headphones. Even among the war surplus equipment there was little of real value. The OSS technical staff had concentrated its efforts on creating special weapons and explosive devices for equipping partisan forces and operatives behind enemy lines. Few of the wartime agency’s resources were devoted to technical aids for agent operations and even less to developing eavesdropping equipment.24 The U.S. Army Signal Corps had produced a bugging kit but, at more than a decade old, it was sorely outdated.
While some equipment such as microphones and amplifiers was available on the commercial market, these devices were bulky and generally not suitable for covert duty. As a result, the Agency’s supply of devices was limited to obsolete military surplus and whatever Kurt and his colleagues could scrounge, assemble, or modify from the telephone company or recording industry.
There was also little experience among the TSS staff. Most of the engineers, like Kurt, were just out of college, and in their mid-twenties or a little older if they had served in the war. The older TSS engineers’ wartime experience tended toward equipment like radar, sonar, and large shipboard systems rather than clandestine audio surveillance. It would take the young engineers time, and trial and error to learn the new business of covert audio operations. And the world was on the verge of a technological revolution that put them in the right place at precisely the right time.
In 1947, scientists at Bell Labs demonstrated the germanium transistor and patented it the next year. By 1952, transistors were being used in specialty devices, such as hearing aids and military systems. Two years later, Texas Instruments, along with a small Indianapolis company, I.D.E.A, introduced the first transistorized “pocket radio.” Called the Regency TR-1, it sold for $49.95 and appeared in stores just in time for Christmas.25 The age of the transistor had arrived.
Through these electronic miracles, everyday consumer electronics could now be made smaller, less power hungry, and more reliable. For clandestine operations, the transistor’s impact would prove equally profound. The same transistor—“solid state”—technology that allowed teenagers to listen to Elvis at the beach would provide the foundation for new capabilities in audio surveillance operations. Yet the transistor solved only half the problem for the CIA. TSS still lacked the necessary in-house laboratory facilities and engineering expertise to conduct basic development work, and the funding to pay for it. In response, TSS revived the OSS model of forming classified partnerships with industry and academia to develop technology, then contracting with companies to design and produce the systems.
In the booming postwar economy, competition was keen and companies were adding R&D engineers as fast as they could in an effort to feed industrial and consumer markets hungry for innovation. The decision to use classified contracts with private industry seemed a practical way to get the maximum “bang for their buck,” or in this case, the smallest, most efficient audio devices for the dollar. TSS eagerly adapted new technologies from commercial research as well as spin-offs from the larger government programs to meet its operational requirements.
Because of the premium placed on reliability for clandestine devices, TSS bet that conventional and proven equipment, like transistors, microphones, and recorders, which worked well in the consumer and commercial markets, could be repackaged, reduced in size, and adapted to covert use. The same assembly processes used for making consumer products could also be redirected toward the production of spy gear.26
Companies that lent staff to the OSS during World War II were now asked by TSS for access to their proprietary research and their best engineering minds. At times it was a tough sell, just as it had been for Stanley Lovell. TSS was not as lucrative as the “big ticket” items like satellites, radar systems, missiles, submarines, and airplanes. The needs of TSS were relatively small—decimal dust—compared to billion-dollar military and satellite procurement programs. The CIA did not need production runs of 10,000 or 50,000 units. Fifty or a hundred small, reliable devices were enough and the companies could not publicly acknowledge or promote what had been produced. For large companies, in particular, these contracts and their limited production runs were marginally profitable in the short term and offered little potential commercial payoff over the long term.
Budgetary troubles severely limited TSS’s audio program in the early years. One tech remembers the entire budget for worldwide audio equipment in 1956 was under $200,000, enough to buy a few tape recorders, microphones, and some other commercial equipment, but not nearly enough to mount either an effective engineering effort or aggressive operations. Many of the new prototype devices developed by private contractors and research projects never left the labs because TSS simply did not have the funds to order even a small production run.
Then in 1957, a CIA Inspector General (IG) report addressed the issue of whether audio surveillance would be a core CIA mission and a primary future method of collecting intelligence. The report urged the DDP and TSS to make audio operations a “top priority” and forever changed TSS’s financial picture.27
A post-World War II engineer working in the audio equipment branch at the time, Tom Grant recalled that soon after the IG’s report was issued, he received an unannounced visit from a senior CIA official. Asked about the state of audio surveillance equipment, Grant replied that both he and the research staff were frustrated and then outlined the problems in detail. For instance, when lab equipment broke down, Grant explained, he could not order a new unit because the limited funds available were needed for gear to support ongoing operations.
The visitor listened for some time, and then abruptly concluded the conversation by saying, “I’m willing to authorize ten times your current budget.” Grant immediately renamed his guest “Mister Moneybags from Headquarters.”
The additional funding, for a new program code named EARWORT, arrived in increments as TSS spent it.28 To the techs, it seemed as if the financial floodgates had opened. Grant’s job turned from scrounging the cheapest equipment possible to talking with development engineers about new mechanical and electronic devices to aid clandestine operations and ordering the most promising. Not every item was successful when put to operational testing, but at long last TSS was seriously in the audio surveillance game.
With new equipment coming online, the need for trained engineers to deploy and service the systems around the world was evident. Prior to 1958, TSS had only a handful of technical operations officers capable of planting bugs and setting up listening posts where the audio take was initially processed. 29 Tech equipment, cameras, microphones, and recorders were typically issued to case officers in the same way as concealments and one-time pads. TSS received an “equipment order,” and then delivered the devices to the case officer along with some basic instruction.
However, the new, more complex—and delicate—devices brought with them the need for an increased expertise. For example, the first over-the-air audio transmitters incorporated glass vacuum tubes in their amplifiers, requiring special care in handling. Something as simple as a bumpy ride in the trunk of a car could play havoc with tubes mounted on a galvanized chassis amid the internal bird’s nest of wiring. If a case officer opened a crate containing a large reel-to-reel tape recorder and found it did not work “out of the box,” the entire system was shipped back to headquarters or a tech dispatched to troubleshoot the problem.
No body of knowledge, experience, manuals or testing protocols, either in-house or with the contractors, existed for those early systems. TSS had no method of documenting or benchmarking electronics destined for clandestine operations. The development and deployment processes were ones of trial and error—with a host both of trials and unforeseen errors. The most frustrating challenges were with technical devices that worked perfectly on the test bench, but then failed when installed for an operation.
In one early mishap, modified reel-to-reel tape recorders intended for telephone taps were designed to accommodate the waiting period between calls by turning the machine off when the line was not in use. In concept, this innovation saved recording tape, limited the need for constant monitoring at a listening post, and improved the efficiency of transcription. The recorders would start when the call began and switch off when the call ended. In testing, the system met the engineering requirements. It was only after deployment was a serious problem recognized. Neither the manufacturer nor the Agency anticipated the long wait times between calls. When a call ended, the recorders turned off the motors that advanced the tape, but did not disengage the magnetic heads. The recording heads, it was discovered, heated up after long periods in the pause mode and eventually melted the motionless recording tape pressed against them.
For an engineer, this was a small problem easily solved with a screwdriver and a quick change of relays to retract the head from the tape when not recording. However, for a nontechnical case officer in South America, the only solution was to call for a traveling tech to change the relays of each recorder at each station.
The installation of concealed listening devices sometimes unintentionally pitted the case officers against the techs. No technical skills were required for a case officer to pass a one-time pad and shortwave radio along with instructions for its use to an agent. However, the most basic mic and wire operation, which generally included concealing a microphone, tapping a power line, and running the wire back to the listening post, required a level of technical expertise beyond the typical case officer.
While the case officers designed the nontechnical elements of every operation, their limited understanding of the technical requirements for a successful installation did not pass without notice. “What are the two biggest lies techs tell?” went the question, followed by the punch line, “The time of my commute to work and the amount of time we tell the case officer the installation will take.”
Most problems boiled down to understanding the capabilities and limits of the technology. Nontechnical case officers, seeing new technologies emerging in the 1950s and 1960s, were prone to either underestimating capabilities or overestimating benefit. Impractical operations proposed by case officers soon became part of the unofficial lore of techs who diplomatically described the most fanciful of these operations as “high-risk options.” One courageous case officer suggested a bugging operation that would have had him lowered by helicopter onto the balcony of the target’s apartment in a major European city. Although dramatic—even movie worthy—it failed the basic audio operational standard that surreptitious entry be clandestine. A helicopter hovering in central Madrid with a case officer dangling from a rope ladder would likely be noticed. Another proposal involved a tunneling operation in which the managing case officer suggested that the tons of dirt and debris generated could be flushed down toilets and carried away by the city’s sewer system.
The growing awareness that technical devices offered enormous potential for intelligence collection demanded a new type of case officer-technical officer interface. If case officers were not qualified for the technical phase of most operations, engineers in the lab were equally untrained and unsuited in the basic tradecraft required for field operations. Laboratory engineers had neither the training nor experience to plan surveillance detection routes or select usable dead drop sites.
As more audio operations were conducted in the 1960s, case officers and audio techs found themselves dependent on each other’s skills. Audio techs planting bugs were often in apartments without the knowledge of the resident or on the property of another government. They usually worked under time constraints and the stress of possible discovery. Mistakes and miscalculations were costly because second opportunities for an entry were rare and no traces of their work could be left behind.
Installations of audio devices also frequently called for technical improvisation when the operation was not accurately described in the planning phase or if equipment simply failed.30 Troubleshooting a short-circuit in the bug with a voltmeter at 0200 hours in the basement of a foreign consulate, then cobbling together a fix from a limited selection of spare parts required a special personality. What the Agency needed was a hybrid of the technically oriented, creative, street smart, and pragmatic individual who thrived on adventure.
TSS cast its net wide, seeking out likely recruits among telephone companies, military bases, technical schools, and commercial radio stations along with the emerging television industry. They placed ads in popular technical and science publications without identifying the prospective employer. 31 While these first tech recruits may not have known how to design a new audio device from scratch, they knew how to read a schematic and their way around a soldering iron. They were natural tinkerers who grew up taking radios and cars apart, and then putting them back together. As kids, they played with erector sets and read magazines like Popular Electronics. Several were amateur radio operators who understood the basics of transmitting, antennas, and frequencies.
Grant’s entrance into spying was typical of that first class. In 1952, he graduated from an electronics school in Kansas City and found a good job as a video engineer at the New Orleans television station WDSU. Then, a few days after receiving his draft notice, whether coincidentally or with other knowledge, a CIA recruiter called with an offer. Although he had turned down the recruiter once before, Grant now responded enthusiastically, took the job, and went on to serve in TSS, TSD, and OTS for more than thirty years.
The intelligence contribtution of techs like Grant, who thrived on fixing and experimenting with electronics, was imperfectly understood by the Agency’s senior management. Dr. Herbert Scoville, the Deputy Director for Research in 1962 and 63, reportedly referred to TSD as “those tinkerers” at a staff meeting. The patronizing label received wide circulation within TSD and served to reinforce the techs’ identification with the Directorate of Plans rather than with the new Directorate of Research.32
There was virtually no legacy of experience and TSS engineers and technicians received little or no formal training in audio operations. Whatever clandestine expertise they acquired occurred on the job. Many of these techs were technically intuitive and given to modifying consumer electronics for their clandestine work.
On an assignment overseas in the early 1960s, at a time when public address systems were often built into classrooms, offices, and hotels, a newly deployed tech realized the job of bugging every room in a large hotel was beyond the scope of a single person. However, within hours he had jerry-rigged a small circuit that turned the rooms’ wall-mounted speakers into passable microphones that picked up conversations at the flip of a switch.33 The innovation had security advantages beyond efficiency since the room speakers (usually used for announcements and fire alarms) were part of the woodwork and ignored by patrons.
Wall-mounted speakers were not the only type of in-place speakers whose wiring could be reversed. Television sets and table radios could be wired so that their speakers, when not in use, were turned into microphones. The techs could use televisions and radios as concealments for small microphones hidden behind the cloth or grill in front of the speaker. With the transmitter’s circuitry masked by existing wiring, the audio device drew power whenever the set was plugged into an electrical outlet.
When a tech was directed to bug an apartment but could not enter it nor drill through the wall or ceiling to create an air passage, the solution came in the form of a contact microphone. Working on the principle that all hard surfaces in a room vibrate in the presence of voices and noise, placing a sensitive contact microphone on the reverse side of a wall or floor would pick up these vibrations and feed them to an amplifier and tape recorder. The design of the mic was similar to a traditional phonograph cartridge with the needle removed. The tech could hollow out a small furrow in the floor of the apartment above the target, place the microphone in the groove, and cover it with putty to eliminate ambient vibrations.
“Audio techs had to have a little larceny in their hearts to master skillsneeded in the field, including picking locks, duplicating keys, tapping phones, and surreptitious entry, to gain access to the target sites. Did we do anything illegal?” Grant recalled. “I guess, most of it.”
MAKING THE KEY IMPRESSION
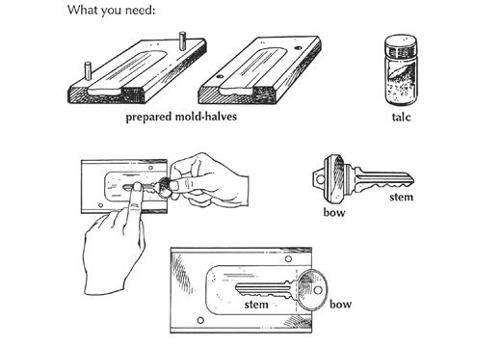
Use of a Key Impressioning Kit was often the first step in copying original or master keys for surreptitious entry into buildings and rooms.
Arriving in South America in 1958, an audio tech prepared for an operation to bug the trade office of an Eastern Bloc country. These government-controlled trade offices, functioning primarily outside the diplomatic community, posed as Western-style commercial companies and provided convenient cover for the intelligence officers.
The Soviets used both Amtorg, a trading organization, and Aeroflot, their national airline, as covers for espionage. From Amtorg offices, the Soviets conducted industrial as well as political espionage. Throughout the Cold War, the Soviets sought America’s advanced technology by targeting individuals in private companies. In one year alone, the Soviets’ New York residency supplied more than 180,000 pages of classified and unclassified documents along with samples of state-of-the-art technology.
It was a smart way to operate in the West since a business cover of “furthering peaceful trade and commerce” offered access to the latest manufacturing equipment and technical expertise, proximity to scientists and engineers who might be recruited, and a platform from which to recruit in nearby countries. In developing countries where business and politics frequently intertwined these front companies proved the ideal conduit through which Western economic and scientific secrets could flow back to Moscow. 34
Not surprisingly, these commercial offices were priority targets for Agency audio operations. A microphone installation, taps on phone lines, or a telex intercept could yield high-value intelligence about local operations, sources, and recruited agents. Making commercial offices even more attractive was the fact that they were generally less well protected against intrusion than diplomatic facilities. To maintain the façade of a legitimate business, the trading companies leased office space in commercial buildings with security that usually conformed to local business practices. In some instances, the CIA officers would lease space directly above, below, or to the side of these Soviet offices, giving techs a common wall for audio ops.
In the South American country, the target trade office was located in a six-story commercial building in the heart of a major city. Erected before World War II on a main thoroughfare, the building was otherwise unremarkable. Arrangements were made by the local station to rent a small office in the same building to serve as a front.35 The tech, posing as an employee of the front company, began his technical survey of the building’s structure, architecture, layout, and entrances in preparation for an installation.
The tech found the stairway door leading to the roof and attic when, unexpectedly, the building’s porter appeared. “In my best broken Spanish, with a big smile and plenty of hand waving, I said, ‘Hey, how can I get up to the attic—there are many windows up there that overlook the city,’” the tech recalled. “‘I’ve noticed how many beautiful churches you have and this would be a wonderful place to take pictures. I want to photograph as many of your churches as I can.’”
The porter, growing misty-eyed, gestured for the tech to follow him. With his new escort and communicating as best he could on their trek to the roof, the tech encouraged the porter to show off every possible aspect of the building, stairways, entrances, offices, and crawl spaces. When they finally reached the top floor, the tech found the attic appeared permanently unfinished, consisting largely of unused space with the partially completed floor offering clear access to the ceilings of the target suite. In short, the vacant attic was the ideal point to plant bugs exactly above the target and an easy way to run concealed wires back down to the listening post in the Agency’s rented office several floors below. The tech took a few pictures from the attic window, thanked the porter (again in his best broken Spanish), and left.
Returning the next day with a high quality 8 × 10-inch photograph of the church across the street, the tech presented the image to the porter along with a small gratuity. The porter was so pleased he invited the tech back to take more pictures. With the porter an unwitting source for authorized access, the tech now had plausible reason to be in the unoccupied spaces of the building for extended periods. On the third day, the tech returned with his bag of tools, microphones, and wire, along with a more sophisticated photo system that included a large Speed Graphic camera and tripod.
Positioning himself in the attic directly above the ceiling of the target office, the tech set up his tripod, mounted the camera, and pointed it out the window in the general direction of a church. On the floor was one of the microphones the tech camouflaged to look like a foot switch with a cord running to the camera. As the tech was about to begin drilling through the floor for the microphone implant, he heard footsteps on the stairs. Quickly repacking his audio equipment, he found himself face to face with the porter, accompanied by his entire family, who came in to watch the American take pictures of the city’s churches.
Clicking the camera, the tech explained that today he would be doing “time exposure” photography that required several hours to complete. After politely watching the camera and the tech for a while, the family became bored and left. With the porter and his family gone, the tech positioned the mic above the ceiling of the target’s office and ran the wire from the microphone through the building’s ductwork to the listening post where recorders would be installed. “It worked like gangbusters and, for all I know, it might still be there,” the tech recalled proudly decades later.
Before 1960, bugging operations were primarily “mic and wire jobs” with techs running wires from the implanted microphone to the nearby listening post. In cases where wire could not be run out of a target facility, a concealed recorder was installed and tapes were changed regularly by a support asset, such as a recruited secretary or custodian with access to the target. What the Agency needed was a reliable radio signal transmitter from the target to a listening post.
There were advantages to each system. The clandestine transmitter eliminated the need to run wires, but usually required regular battery replacement, and the radio signal was vulnerable to sweep teams. The mic and wire jobs were difficult to detect since they did not emit a radio signal, but the wires took longer to install, and were susceptible to discovery during a physical inspection of the premises.
In 1963, a case officer arranged for the techs to have access to a Soviet Bloc residence while the diplomat was out of town. The operational plan was to embed mics in the concrete wall of the house, but when the techs began drilling they discovered their hardware store drills were ill suited for the task. They made too much noise for middle of the night work. The techs determined that liberal lubrication at the drilling point would dampen some of the sound and the next day a support officer was sent to the U.S. commissary to buy several gallons of Crisco cooking oil.
After dark, the techs returned to the job, and repeatedly dipped the drills into the Crisco to keep the hole lubricated. They were rewarded with much quieter drills, but as the drill bits heated in the deepening hole, so did the oil that coated them. Soon the poorly ventilated house was filled with the odor of fried food, posing a serious operational compromise should the residents unexpectedly return home.
While the drill team worked on the wall, two other techs were running the microphone wires across the diplomat’s immaculately tended garden and manicured lawn to the nearby listening post. Working only with the available light provided by the stars and moon, the techs dug a shallow trench by hand using bayonets. It was tedious work. Not only did they have to stay on a course plotted across the wide expanse of lawn and flowerbeds in the dark, they also needed to carefully pick up any loose dirt on the grass and replace each piece of sod or flower as they moved along. Progress moved at a snail’s pace as the techs spent the last hour of every night erasing any sign of their presence on the lawn.
“There was a very conscientious gardener who took care of the landscaping,” one of the techs recalled. “We installed an observation post where we could watch the house during the day in case the diplomat returned early or visitors showed up. We began noticing that every morning, when the gardener came to work he’d walk over to the flowerbed where we’d been working, look down, shake his head, and go on about his business.”
Panic began to spread among the techs and case officer. Had the gardener noticed the trench and was biding his time until the diplomat returned to tip him off? The restoration of the lawn looked flawless to the techs, but perhaps the professional gardener noted a disturbance or saw traces of the narrow channel they dug for the wires. Each day the gardener continued to inspect the flowerbeds with a worried look, but refrained from poking around in the grass. Finally, the case officer decided the only choice was to attempt to recruit the gardener since he clearly had noticed something amiss.
The plan worked. After the gardener agreed to a covert relationship with the CIA, he heaved a great sigh of relief. “Every morning for the last week,” he said, “I come to work and the red flower would be where the yellow one used to be, the blue one was over here.” Because of darkness, the techs did not always recognize the color of the flowers they replanted after digging, and inadvertently rearranged some of the plants. Reassured that he was not losing his mind, the gardener kept the secret and the installation operation came to a successful end.