CHAPTER 19
We have slain a large dragon but we now live in a jungle filled with a bewildering variety of poisonous snakes . . .
—R. James Woolsey in Congressional testimony after the collapse of the USSR
The Agency’s war against terrorism began decades before September 11, 2001. The CIA’s chief in Athens was assassinated in December 1975. In October 1983, terrorists used a truck bomb to blow up the Marine barracks in Beirut, murdering 241 U.S. soldiers. That same year, terrorists bombed the U.S. Embassy in Beirut, killing 63, including CIA officers. Then in 1984, CIA’s chief in Lebanon, William Buckley, was kidnapped, tortured, and later murdered in 1986. That same year, DCI William Casey created the DCI Counterterrorist Center staffed by representatives from the principal intelligence community agencies, with a mission to “preempt, disrupt, and defeat terrorists.”
While radical groups with diverse agendas, such as the Baader-Meinhof Gang, the IRA, and the Weathermen, committed terrorist acts during the 1960s, America saw the face of terrorism up close during the 1972 Olympics in Munich. Broadcast live on international television, the dramatic scenes of masked Palestinian terrorists killing eleven Israeli athletes seemed as senseless as it was shocking.
To the CIA, the only new aspect of the appalling spectacle in Munich was its global broadcast. Acts of terror carried out by religious and political fanatics, either independently or with government sponsors, have influenced societies and destabilized governments for centuries.1 In the eleventh century, a Muslim sect, the Order of the Assassins, conducted suicide missions with the promise of “paradise to follow.”2 English Catholics conspired to blow up Parliament in 1605 in hopes of creating an uprising against King James I.3 The list of terrorist acts through history includes virtually every country and continent. However, in the last half of the twentieth century, the frequency of terrorist strikes accelerated dramatically. According to one account, 8,114 terrorist incidents occurred worldwide during the 1970s. In the 1980s, that number increased nearly 400 percent to more than 30,000.4
Advances in technology have aided terrorists in their efforts. New chemistries have reduced the amount of explosives needed to inflict significant damage, and television coverage typically allocates airtime relative to the number of people killed or injured. It can be argued that the net effect motivates increasingly more heinous acts in an attempt to attract the attention that drives public fear.
Targeting civilians is a fundamental terrorist tactic. In the nineteenth century, the radical German revolutionary Karl Heinzen envisioned a time when weapons of mass destruction, powerful enough to destroy entire cities, would be in the hands of terrorists.5Stopping that from happening became one of CIA’s most important missions.
The first OTS officer assigned to Vietnam, Pat Jameson, may have been the first OTS tech drafted into the war on terrorism. During the early 1970s, terrorists were using tools already well known to Jameson, including false identities and documentation along with special weapons and improvised explosive devices. His experiences in Vietnam and Laos with target analysis and planning paramilitary operations allowed him to understand how terrorists identified target vulnerabilities and traveled undetected.
When the United States left Vietnam in 1973, OTS reassigned Jameson from Laos to one of its covert European bases. Now a seasoned tech with experience in both paramilitary and audio surveillance operations, he would become a primary Agency resource for creating counterintelligence programs in Europe and Middle Eastern countries. Early counterterrorism operations concentrated on putting audio devices into residences and offices of suspected terrorists. The strategy, Jameson recalled, “paid off handsomely,” particularly in West European countries where members of terrorist cells were often longtime residents and believed their radical activities were protected. For the Agency, these operations not only assisted countries in preventing attacks, they also provided a means to solidify and expand cooperation with local security services.
Jameson found that many Middle Eastern countries were overly confident in their attitudes, thinking themselves immune from terrorist acts. Several countries, including friends of the United States, ignored or failed to take action against terrorist groups at home, as long as they conducted their attacks elsewhere. In late 1974, a CIA chief invited Jameson to assess one country’s overall counterterrorism security picture. He confided that his contact, a general who headed the local intelligence and security service, seemed unconcerned about the potential for terrorist attacks on the government. In keeping with a tradition established by Donovan and Lovell, Jameson and his counterpart spent an evening drinking good brandy and devising a plan that would form the country’s first counterterrorism program.
A few days later, Jameson secured a meeting with the general, intending to offer a special training program for a new counterterrorism team. However, upon entering the general’s office, Jameson faced an unreceptive host despite the recent problems in the country from a foreign terrorist cell. The general dismissed the incidents as insignificant and isolated and remained adamant that the country had no terrorist problem that needed CIA assistance.
Jameson saw an opening. “Well, that’s good,” he responded, “but I have a bet for you. I believe I can walk down to your marketplace, make a few purchases, and within a few days create an explosive device that I can then plant in a public location to kill any important foreign guest that comes into this country.”
The intelligence chief nearly exploded with anger. Jameson had challenged his fundamental responsibility, the protection of the country’s leader, and his international guests. Several minutes passed and when the conversation calmed Jameson suggested that the general personally choose one of his officers to accompany him as a guide and translator for a few days to prove or disprove his bold wager.
During the next three days, Jameson and his guide wandered the markets of the capital city and purchased remote-controlled model airplanes, ammonium nitrate fertilizer, diesel fuel, and parts to make improvised detonators—everything necessary to make a powerful bomb.6 Jameson then checked into the hotel directly across the street from the intelligence chief’s office and spent two days observing and making notes about security at the hotels, on the streets, and at entrances to government buildings.
Returning to brief the general, Jameson was greeted with a slight smile. “So, you wasted your time, didn’t you? You see, we’re really secure here,” the intelligence chief said. Jameson pulled a small U.S. government-issued green-covered notebook from his pocket and began reading from his notes.
“I bought radio control switches to activate a bomb. I bought ammonium nitrate for the explosive. I bought a tourist suitcase to hold the bomb,” he recited. “I bought fuses, timers, and initiators. Here’s a list of the prices I paid for each item. I can get as many as I want. I can make one or several bombs and I can make a big one or a small one. See, it’s all here and your man knows that I have it all in my hotel room.”
The general remained unconvinced. “That might be so, but you can never use it operationally here,” he said. “You could never get close to my VIP guests.”
Jameson was prepared. “Sir, look outside your window. There’s a big sedan parked across the street right in front of the hotel where all your guests stay. I would load that car up with explosives, sit on my balcony, and wait for your guest to come out. I’d push the button and boom—no more VIP.”
The general was stubborn. “No, that wouldn’t work either. My security guys are well trained, well armed, and know how to protect VIPs. They would spot anything out of the ordinary like that car.”
“We’ve checked,” Jameson shot back. “That car hasn’t been moved for three weeks.”
The intelligence chief agreed to consider what Jameson had reported.
Included in Jameson’s final security report was an item that would prove eerily prophetic. It warned of the dangers posed by a longstanding tradition in the country whereby petitioners could ask the head of state for assistance by pleading their case in person. Jameson assessed the vulnerabilities of the petitioners’ ceremony and concluded that a high probability of assassination against the leader existed. He noted that petitioners approached the ruler one at a time without being screened, searched, or x-rayed. To emphasize the point, he added that close associates and extended family members had nearly unrestricted access to the head of state. Nothing would prevent one of these from carrying a concealed pistol and shooting at close range.
While that portion of Jameson’s report was ignored, other pieces of a U.S.-proposed counterterrorism program began falling into place. The general understood the vulnerability presented by the example of the unidentified automobile parked near his office and a few weeks later a commercial airplane with its windows covered with blackout paper landed at a covert CIA training site. The passengers were members of a special counterterrorism and VIP-protection team sent by the general for a month of intense training by OTS specialists. As the team disembarked, Jameson personally greeted each one. Now having proved himself a friend of the country, he began having regular meetings with the general to offer advice and planning assistance.
In the mid-1970s, after completing one of his now frequent meetings with the general, Jameson headed home. During a stopover, as he approached the boarding gate to catch a connecting flight, he was surprised to see another CIA officer waiting for him. The general was demanding that Jameson return immediately. The country’s leader had been assassinated.
“Let me guess. He was holding an audience, the people were standing in line and he was sitting there talking to one of them and they shot him in the head,” Jameson said.
“How do you know that?” the colleague asked, taken back by the specific details.
“I told the general six months ago that could happen. I didn’t have a premonition. But I saw how the petitioners approached and how he was unprotected from his inner circle, the risk was obvious.”
“You were right. The assassin was a relative.”
Jameson knew he was in a delicate situation. Not only had the assassination occurred uncomfortably soon after his report, but he had just departed the country hours before the shooting. If the general believed he was somehow implicated in the murder, Jameson could be arrested the instant he stepped off the plane. On the other hand, if Jameson didn’t honor the request to return, they might assume that he, along with the CIA, was guilty of something.
Jameson spent a sleepless night in limbo as cable traffic was exchanged with Headquarters. All eventually agreed that it would be best for the OTS officer to go directly to the general, tell what was known, and offer personal as well as Agency assistance.
It was not a comfortable meeting. The general launched a tirade about the ineffectiveness of CIA counterintelligence training while implying that Jameson might have had some connection with the assassination. Letting the accusations pass without comment, Jameson replied, “I told you how I would go about doing this, I didn’t say I was going to do it. I told you what was needed to correct the situation, but you didn’t correct it. What has happened is past. Where do we go in the future?”
“You stay here for now,” the chief ordered, concluding the meeting.
After several days of being under virtual house arrest, Jameson requested another meeting. The general had calmed down and conceded that no blame for the assassination lay with Jameson or the CIA. He was free to leave the country. However, for the remainder of his career, Jameson would be part of CIA’s counterterrorism mission and within a few months tragedy struck first hand. In December 1975, Jameson’s CIA chief in Athens, Richard Welch, died from a terrorist’s bullet.
Among terrorists’ standard weapons are small amounts of explosives fashioned into improvised devices and concealed in everyday items. Although small, these bombs can create physical damage as well as instill fear in a larger population. Less than an ounce of explosive is needed for a letter bomb capable of killing or maiming anyone around it. A few pounds of explosive hidden in a purse, briefcase, or suitcase can bring down an airliner, while a few hundred pounds in a car or van is capable of destroying an entire office building or embassy.
Bill Parr had a cramped office in Southern Europe during the late 1970s but that mattered little since most of his work was on the road. As one of the few OTS “bomb techs,” Parr frequently received the first call after bombings in Africa or the Middle East. CIA stations found that after bombings foreign services were especially receptive to hosting techs like Parr who knew how to conduct post-blast investigations and analyze security weaknesses.
Parr was asleep at home when a phone call awakened him at 2 AM. “Come in immediately.” The caller did not need to identify himself. Parr recognized the urgency in the voice of the CIA’s senior communicator. Arriving at the office, Parr saw the message headed with the word IMMEDIATE and followed by NIACT, for “night action,” which required an immediate response regardless of the time of day.
This message originated from a country friendly to the United States, and whose political leaders were frequent targets of terrorists. Reportedly, the country’s intelligence chief had acquired what seemed to be a suitcase bomb from a terrorist cell. For reasons unknown, the intelligence chief had taken the suitcase to his office, opened it, and noticed wires in one corner along with some unidentified materials wrapped in black tape.
“Then he apparently suffered a sudden attack of brilliance and decided not to mess with it anymore,” Parr recalled. “That’s when he called the CIA for help.”
Parr replied with his own IMMEDIATE-NIACT with questions about the appearance of the device and remained at the office for the rest of the night responding to additional messages before catching the morning flight out to see the device in person. Reaching his destination before noon, Parr was taken to an office where the opened suitcase sat on a desk. Almost certainly a bomb, the suitcase contained a messy collection of wires, small boxes wrapped in black tape, and miscellaneous packing materials. When an x-ray machine was located at a nearby prison, the suitcase was carefully transported there. The x-ray image revealed a coil pattern in one of the taped packages that Parr concluded was detonator cord wrapped around another unidentifiable substance, probably high explosive.
The trigger mechanism to control the detonation was circuit board wired to the coil. Parr calculated that he could pull the electronics away from the explosives without initiating a detonation. Taking the device to a remote area, he attached a hook on a long line to the electronics, and gave it a hard yank from a safe distance. The electronics, which had been attached to the blasting cap with black tape, pulled cleanly away from the explosives. After cutting off the blasting cap, he x-rayed the device again to recheck the circuitry.
With the device rendered safe, follow-up operational ideas began emerging. The bomb had been obtained through an agent who penetrated a terrorist cell. If a signaling device could be attached, and the suitcase reinserted into the cache, it could be tracked to determine its intended target. However, to do so, the bomb would have to be reassembled.
Parr knew that since he took it apart, he could put it back together, but the agent had only a few hours to return the device to the cache before someone discovered it missing. Not only did that rule out a tracking operation, Headquarters, quite sensibly, disapproved of returning a live bomb to a terrorist cache. The tech would have to reassemble a disabled bomb without leaving any traces of tampering. Using a layer of epoxy to short out the wiring from the switch to the blasting cap was relatively simple, but reassembling the bomb in its case without leaving signs of alteration required several hours. The sleep-deprived tech finally completed the reassembly and delivered the bomb to the local service for return to the cache. Sometime in the future at an unknown time and place, a terrorist’s plot would fail.
In the course of disassembling and reassembling the components, Parr examined the electronic circuit board, took photos, and made sketches. The device contained components he had not seen in terrorist devices, revealing a new type of timing device that subsequently appeared in other bombs as a trademark for a particular PLO bomb maker.
“You deserve a medal,” the chief told Parr as he departed.
“I don’t think so,” Parr replied, “I’ve spent most of my life in Vietnam and Laos making devices that help kill people. It seems a little ridiculous to give me a medal when I disarm a device.” Nevertheless, a few months later, based on the recommendation of the chief, Parr did, in fact, receive the CIA’s Intelligence Star for “a voluntary act of courage performed under hazardous conditions.”
In December 1988, John Orkin was heading an OTS unit responsible for conducting technical design and performance assessments of spy equipment deployed against American targets by the Soviets or other adversaries. These devices were usually discovered either through technical surveillance countermeasures or acquired from a friendly liaison service.
Typically, Orkin’s engineers analyzed each recovered device to determine its country of origin, function, materials, design, and capabilities. This was no easy task, since intelligence organizations routinely mask the country of origin of a device by “sanitizing” spy gear. Since a bug found in the wall of a diplomat’s office was not usually stamped MADE IN THE SOVIET UNION or came with an instruction manual, Orkin’s job was to figure out how a mysterious device worked, who made it, and how it might have been deployed.
With a well-equipped suite in the sprawling OTS covert laboratory outside Washington, Orkin joked that he was far enough from the Langley Headquarters to do “real engineering work” without interruption or micro-management. The lab was largely immune from the crisis-to-crisis atmosphere that dominated many intelligence operations.
Orkin began his CIA career during the early 1970s evaluating OTS equipment. Responsible for testing every piece of spy gear produced by OTS before certifying it for deployment to the field, the unit functioned as the Agency’s in-house “Underwriters Laboratory.” Far removed from the glamour associated with agents, spies, and back-alley intrigue, testing the frequencies of transmitters and battery life of communication devices in a government laboratory seemed a world away from the frontlines of espionage.
The certification of OTS devices and analysis of hostile gear involved both elements of reverse engineering and similar testing procedures. However, during the 1970s, analysis of foreign devices was an ad hoc affair. “As a device was recovered the lucky engineer-of-the-day got assigned the project to test and write a report on how the foreign equipment performed,” explained Orkin. “We were dealing with mostly technical surveillance equipment—microphones, transmitters, communication and concealment devices. Eventually it became apparent that we were reinventing the wheel with each analysis. When a device came in, we often didn’t remember if we’d seen the same thing three years before or if there was already a report in the file. So, one of the engineers finally said, ‘Give them all to me. I’ll do the work.’ Over time he became the in-house repository of knowledge about foreign equipment.”
Eventually, this led OTS to establish a unit with expertise in reverse-engineering foreign equipment and a proficiency in spotting patterns that accompanied technological evolution. Although the number of new devices might be fewer than ten a year, analysis was needed to establish continuity. “We needed to develop data to do a side-by-side comparison to look at the evolution of devices,” he said. “We needed to know with certainty if two devices were identical and, if not, then document the changes and record the improvements.”
The Soviet Union remained the focus for OTS foreign-equipment testing well into the 1980s. The work analyzing Soviet and East European spy devices offered invaluable counterintelligence data for the FBI, State Department, and U.S. military security components that were also developing countermeasures.
However, with the number of terrorist organizations multiplying in Africa, Europe, the Middle East, and Asia in the 1970s, the Agency began acquiring explosives and bomb fragments from terrorist caches and post-blast investigations. As most early terrorist bombs were individually fabricated from whatever parts and materials the bomb maker had at hand, these were collectively known as Improvised Explosive Devices or IEDs. The OTS expertise in reverse engineering and knowledge of foreign electronic circuits proved to be the perfect match for unraveling the firing, triggering, and timing mysteries of these weapons. It was in this way, almost by accident, that Orkin and his colleagues became the Agency’s focal point for collecting, analyzing, and cataloging instruments of terror.
“The analysis of terrorist devices evolved slowly; it was an occasional item here and there. In fact we initiated some activity ourselves, going to the counterterrorism officers and asking them, ‘What do you have?’ And they’d say, ‘Oh, here’s a device that I picked up in Jordan in 1978.’ And we’d offer to do a report,” remembered Orkin. “Initially we were working backwards on stuff found a few years before. If anything looked like it had been made in more than one quantity or if it looked like something we might see again, we’d take it and do a report on it.”
Orkin began detecting a disturbing pattern of state-of-the-art technology making its way into terrorist devices in the early 1980s. Terror organizations that relied on crude timers and other components for their bombs a few years earlier were now acquiring advanced technology that greatly increased the lethality of terrorist bombs.
“The reason that technology became available was because of state-supported terrorism. Terrorists could buy the needed technology because Syria, Libya, and a few other countries like Iran and Iraq were giving them money,” said Orkin. “Initially they used very simple devices, like timers that you had in your kitchen, alarm clocks, and wristwatches with the hole drilled in the center—they really used the kind of basic stuff you see in the movies. I put 1984 as the date when they began to apply newer technologies to these devices. We began seeing multiple examples of the same device, indicating that they were fabricating them in small ‘production runs.’”
This was a significant turn of events. Terrorists could now get electronics engineers to design the timing circuit for a bomb instead of relying on someone with little training working in his cellar with a soldering iron. Terrorists, who had traditionally been impassioned amateurs, were finding allies, tutors, and funding from the intelligence professionals of rogue countries. Established governments were now directly aiding terrorism by providing cash and enabling networks for procurement and shipment of components and devices.
“Throughout the eighties the terrorists progressed from devices that were fairly simple to those of professional quality,” explained Orkin. “We saw the devices evolve. We would think, boy that’s not a good way to do this, and when the next device came in, we’d see the problem fixed.”
Orkin, an intelligence officer as well as engineer, pinpointed a potential vulnerability that might be exploited. The more advanced and technologically specialized each component became, the more likely it could be traced back through supply channels to specific manufacturers. Embedded in every chip and circuit board were technical and engineering details that, when pieced together, sometimes revealed the genealogy of the device, including its sponsor and even assembler.
For instance, lot numbers denoting manufacturing runs used for inventory control, coupled with standardized fabricating processes, gave virtually every component a personal history. Working out the “technological DNA” of terrorist devices, the foreign-finds experts uncovered yet another disturbing trend: terror organizations were no longer working in isolation. They were now forging ties with rogue nations and each other.
In one instance, when analyzing a device uncovered in the Middle East, he noted features of an elaborate, high-powered radio receiver with British markings. “We kept finding components that were marked from a British company. And when we showed it to the British, they identified it as PIRA [Provisional IRA] technology,” recalled Orkin. “British analysis had concluded that PIRA traded technology for guns and explosives with the Libyans. Libya also trained some of the PIRA guys who handed them the technology. There was another incident in Peru. And when we looked at it, we said this looks like the other device from PIRA.”
What eventually emerged was a complex, interlocking network of terrorist organizations. For example, PIRA technology could support the ETA (Euzkadi Ta Askatasuna) in Spain and ETA could hand off some of the equipment to Shining Path in Peru, and so on and so on. While these groups did not always share political or social agendas, they did share a common desire for bomb-making technology. “It was getting harder and harder to differentiate between groups by their technology,” explained Orkin.
The ringing bells and songs of carolers on Christmas Day 1988 sounded with little joy or peace for families of the 259 passengers and crew of Pan Am Flight 103. Four days earlier, just after 7 PM on December 21, a bomb ripped a hole in the forward fuselage of the Boeing 747 as the plane reached its cruising altitude of 31,000 feet over Scotland. Stunned air traffic controllers at London’s Heathrow Airport watched the aircraft vanish from their radar screens, replaced by small blips as nearly 700,000 pounds of airborne debris, including flaming jet fuel, rained down on the small town of Lockerbie.
Two hundred seventy perished that day, all those aboard the plane and eleven residents of Lockerbie. Death and destruction in the air and on the ground turned the anticipation and joy of the Christmas holidays that traditionally unites friends and coworkers in a spirit of joyous goodwill into a season of mourning. The next day, CIA casualty officers suspended holiday plans after learning that among the dead was a CIA officer. Another star would be chiseled into the white marble of the Agency’s memorial wall of the Original Headquarters Building.
Even for those not directly touched by the tragedy, the grim images of the wreckage on covers of magazines carried a stark reminder that evil honored no holiday. The debris field, spread over more than 800 square miles, was a horrific scene of human remains, personal effects, and pieces of aircraft. The plane had not exploded, but broken apart as it plummeted to earth. Few news organizations captured or broadcast images of the most gruesome elements of the crash site; however, one photo that shocked and sickened the world eventually became a morbid visual shorthand for the tragedy. That was the image of the battered nose section of the 747 with the cheerful script MAID OF THE SEAS resting on its side in a muddy field. Nearly twenty years later, even those who can recall few of the details surrounding the tragedy of Flight 103 remember that image vividly.
Terrorism was not new to the Agency or unknown to viewers of the evening news. Nevertheless, Pan Am Flight 103 seemed different. The plane was not in a war-torn country. Those aboard were students, husbands, and mothers. Their faces, revealed to the world smiling in family photos, showed ordinary lives ended in a violent and grotesque manner. What could the perpetrators possibly hope to gain by murdering college students returning home for Christmas vacation? What message were they hoping to send? The senseless slaughter defied all reasonable motivation and strained even the tortured logic of terrorism.
CIA officials quickly concluded that this was a terrorist attack, even if the identity of the perpetrators and their motives were unknown. Reports from around the world identified groups eager to claim credit for the cruel spectacle. Critical details began emerging over the following weeks, as investigators assembled information from agent reports, signals intelligence, and fragments of the plane. The bomb had been concealed in a commercial Toshiba radio cassette player, the Bombeat (Model RT-SF 16), available in consumer electronics stores. Fragments of the radio, as well as the owner’s manual, were recovered in the wreckage of the cargo container where the blast originated.
Traces of the plastic explosive Semtex were found on the radio’s circuit board and experts calculated that no more than 400 grams (about 14 ounces) positioned close enough to an outer bulkhead was enough to blast an eighteen-inch a hole through the fuselage. Within seconds after the detonation, the plane decompressed, suffered structural failure, and tore itself apart in the sky. But more puzzling than the presence of Semtex or the cassette player was what remained of a brown Samsonite suitcase. Tests revealed traces of Semtex on the suitcase fragments, indicating that it more than likely held the bomb. Yet, no such suitcase was checked in as baggage at Malta, the departure point for the baggage container where the blast occurred and investigators were unable to match the brown, hard-shell piece of luggage to any passenger aboard the plane.
From the start, the investigators focused on the use of Semtex. The explosive of choice among many terrorists, it is difficult to detect, but relatively easy to obtain. Counterterrorism experts suspected Palestinian groups based in Syria, which had used the explosive in past attacks and had a history of relying on consumer electronics as carriers. Iranian terrorists also favored the explosive, a fact that focused attention on an Iranian national aboard the flight’s Frankfurt to London leg, who disembarked before the plane’s departure for New York.
Although investigators understood what had happened, their study of the debris field and wreckage yielded little about who did it and how the bomb had been placed on the airliner. The break did not come for eighteen months. Then, nearly eighty miles from the center of the debris field, a local man stumbled onto the remnant of a T-shirt bearing the label of Mary’s House, a store in Malta’s port town of Sliema. Embedded in the material of the garment was a thumbnail-sized fragment of circuit board, about 0.4 inches square. That tiny speck of forensic evidence would eventually lead to the unraveling of a terrorist plot and test the international justice system.
However, the trail to the Lockerbie bombers began not in a European capital or the Middle East, but in sub-Saharan Africa. The Republic of Chad, a former French colony, is known primarily for the exotic name of its capital city, N’Djamena. Despite decades of ethnic warfare and limited strategic significance in the Cold War, the United States maintained relationships with Chad’s government. In the early 1980s, the local security service uncovered what they assumed to be a case of espionage and quickly moved in for an arrest. When the suspected spy was taken into custody, his suitcase surprisingly contained not a collection of standard spy gear, but a quantity of Semtex attached to a portable radio.
Without the capability to conduct an in-depth technical analysis, Chad’s intelligence service passed the device on to the CIA. The device, Orkin noted, was unexpectedly complex. The sophisticated circuitry was controlled by a standard pager traced to a firm, Meister and Bollier AG (MEBO), based in Zurich, Switzerland. Known to have ties to both Libyan and East German intelligence organizations, the company’s circuits were apparently now being used in a terrorist IED.
A few years later, in the autumn of 1986, local authorities uncovered a terrorist cache of weapons in Togo’s capital, Lome, and U.S. authorities were invited to examine these materials. Among the hodgepodge of aging weaponry and munitions, two state-of-the-art timers stood out, one of which Orkin acquired for analysis. Like the find in Chad, the device was also traced back to Switzerland and MEBO.
Then, in February of 1988, two known Libyan intelligence operatives were arrested in Dakar, Senegal, as they disembarked from their flight. Items found in one of the passengers’ briefcases included a silenced pistol, ammunition, four blocks of TNT, and two blocks of Semtex, along with a timer. Local authorities allowed CIA officers to photograph the timer. The photograph, like the timers from Chad and Togo, eventually landed at Orkin’s lab. Again, MEBO appeared linked to the device.
“In retrospect, the devices from Chad were first-generation,” Orkin explained. “Then, we observed that the device from Togo was a prototype. We said, ‘If you cut the corners out here and change this and change that, you can put it in a box and make it look nice.’ And that’s exactly what we got in the Senegal device, it was a packaged unit.” The terrorists had learned the engineering principles of form, fit, and function.
Orkin now had three increasingly sophisticated devices, all from Africa, all physically linked to the same manufacturer in Switzerland, and all with some Libyan connection. A report on each rested in the OTS archives as technological curiosities of no immediate intelligence value.
Then came Pan Am 103. By September of 1989, Scottish investigators converged on Mary’s House clothing store in Malta, led there by the scrap of T-shirt. The shop’s owner remembered the customer who bought the T-shirt, describing him as a Middle Eastern man who shopped indiscriminately, purchasing items without regard to size, as if he were simply trying to fill a suitcase, which, of course, is precisely what he was doing. The police produced a sketch of the buyer from the store owner’s recollections, though there was as yet no name to go with the face.
The Scots were still having a difficult time identifying the tiny piece of circuit board found embedded in the shirt. Unable to match it up to any piece of the plane or known electronic component, they sent a photograph of it to the FBI with the understanding that it would not be released outside the Bureau. Analysis of the photograph yielded little, if anything, new. After six months, the FBI received permission to show the photo to other U.S. government agencies. That same day, Orkin received an unexpected call.
“The guy calls me from the FBI’s explosives unit. He came out to my lab, pulled out the picture, plus a one-page report with a brief description of the fragment that says it’s epoxy fiberglass and seven-ply board,” said Orkin. “It also makes note of the fact there was green solder masking. Solder masking is used to prevent solder flowing to parts of the board where you don’t want it.”
Orkin had seen the same design before. The green solder masking, coupled with the curve of the board, matched previous reports done on the devices found in Togo and Senegal and associated with Libya. Then he discovered that the fabrication techniques, along with a modified connector, matched the device found in Chad. They all pointed to the Swiss firm MEBO. The connection, though still tenuous, represented a starting point. Beginning with this information about the components found on the African circuit boards, the FBI launched a global investigation.
The FBI traced the components, eventually tracking the timing crystal to a specific company. Asked about the component, the firm consulted its records, which showed that one hundred of them had been sold to MEBO, establishing a definite link back to Swiss firm. Next, the investigators went to MEBO. As Orkin later heard the story, the investigators were told, “Yes, we built ten with the plastic case and ten without the plastic case for the Libyans.” Then, realizing what had been revealed, the manager decided not to talk with the investigators anymore.
Called the MST-13, the timer unit was made specifically for the Libyan government’s Ministry of Defense. The precision device could be set to delay an explosion up to 10,000 hours or 10,000 minutes. “This was an elaborate timer with crystal timing controls that were very accurate,” explained Orkin. “This timer had been in a suitcase placed on a plane going from Malta to Frankfurt. In Germany, the luggage was changed to another flight going to London, and then put on Pan Am 103. It was set to wait many hours before triggering the explosion.”
Based on the recovered evidence, the timer apparently had been set with the intention of sending the plane down into the Atlantic. However, an unexpected weather delay at Heathrow Airport and high winds diverted the flight path over Scotland. Had the plane taken off as scheduled, the bomb would have detonated over the ocean and all evidence likely destroyed or lost forever.
With these discoveries, suspicion shifted from the Syrians and Palestinians to the Libyan government. A defector named two Libyan intelligence officers whom he claimed were behind the Pan Am 103 bombing. The first, Abdel Basset Ali al-Megrahi, was identified as the Mary’s House customer who purchased the T-shirt and other clothing used to fill the suitcase containing the Semtex. The second Libyan, Al Amin Khalifa Fhimah, had a cover job with Libyan Arab Airlines at Malta’s airport. This put them in a perfect position to smuggle the brown Samsonite suitcase into the plane’s cargo hold. The problem for investigators and prosecution was that both suspects were now back in their home country, where Libyan leader Muammar Qadhafi was steadfastly rejecting requests to hand them over for trial.
More pieces of the puzzle fell into place in March of 1990, following the collapse of the Soviet Union. Semtex, the plastic explosive used, was manufactured in Czechoslovakia. The name was derived from the first four letters of the company that first manufactured it in the 1960s, the Semtin Glassworks, plus the suffix “ex” denoting the English word for “explosive.” During a well-publicized press conference in London, Czechoslovak President Vaclav Havel revealed that his country, while under Communist rule, sold an estimated 1,000 tons—2 million pounds—of Semtex to Libya. The Libyans, Havel added, had refused to return the explosives.
By 1992, with evidence pointing decidedly at Libya, the case came before the United Nations Security Council. Sanctions were imposed and negotiations with the Libyan government dragged on for six long years. Then, in 1998, as sanctions became an economic burden, the Libyans finally agreed to turn over the two accused men for trial. The trial was scheduled to take place at Camp Zeist, a former U.S. military base in the Netherlands that had been declared within Scottish jurisdiction for purposes of the trial.
As the prosecution began assembling the case, it became clear the timers would play the key role in linking the two Libyan intelligence officers to the flight. According to Scottish law, the prosecution was obliged to show the defense how the investigators were led to the timing device. This put Orkin, whose entire professional life had been conducted under a cover unassociated with the CIA, in an unusual position. He would appear in open court as an expert witness in an internationally watched trial.
The Agency offered unprecedented assistance in the trial. Not only would Orkin testify, but two former chiefs of station would also be made available, if necessary, to appear in open court. Contents of classified operational cables were provided as evidence.
Orkin’s role was to deliver the critical testimony that linked the devices to Libya, illustrating a technological trail that started in Switzerland, progressed through Africa, and ended, tragically, in a field in the Scottish countryside. He was the single witness who could provide irrefutable scientific credibility to a detective story that began with a minuscule piece of plastic found by chance. But the trade-offs were stark. His presence at the trail could potentially blow his cover and, if he were identified, put his life and the lives of his family in jeopardy.
To protect their identities, the court agreed that Orkin, along with the chiefs, could testify using alias names and wearing tailored disguises. The alias, chosen sometime earlier for the tech who had a reputation for clever puns and elaborate word play—he was “Mr. Orkin,” the bug killer. Whether the Libyans recognized the popular American extermination service was unknown, but as the trial date approached, the key witness became increasingly concerned with his choice of alias. What seemed amusing and fitting at the outset was now worrisome. Could the defense attorneys somehow use the pseudonym to discredit his testimony? Was he being too clever in such a serious matter?
To prepare the witnesses’ disguises, OTS selected a senior disguise officer who combined a sense of artistry to fit the person to the materials as well as match the materials to the subject. It was an exacting process. Orkin needed to not only look natural, he had to feel genuine within the disguise and be relaxed on the witness stand. The obscure OTS engineer would be transformed into the internationally recognized electronics expert “Mr. Orkin.”
The OTS disguise specialist eliminated Orkin’s trademark facial hair, shaved here and added there where previously none existed. “I had a nerdy, old blue suit, white shirt. I almost put a piece of tape on my glasses to finish the effect,” he remembered. “Then there was a stink raised by the Defense lawyers. They said, ‘We don’t want people coming in here in Shirley Bassey fright wigs.’ When we finally sat down with the defense attorneys for a preliminary meeting, after twenty minutes or so of lawyer-type discussion, they asked, ‘Are you in disguise now?’ I was and they couldn’t tell. So much for fright wigs.”
Orkin flew to the Netherlands and met with the prosecutors for a briefing on courtroom procedure. Using technology as evidence and experts to explain it was tricky business. Detailed scientific mumbo jumbo could confuse those without a technical background, and engineers, trained to think and speak with precision, could be trapped by clever legal questioning. For example, Orkin was reminded, a lawyer might ask if a scientific result is “100 percent accurate,” to which an engineer might answer in the negative, because the results were only 99.99 percent accurate. The possibility that the two suspects would escape justice through just such wordplay weighed heavily as the prosecutors prepped Orkin on how to make his data clearly understood in the courtroom.
“We’re going to ask you this, this, this, this, and this, and we’re going to establish your credentials,” the prosecutor told Orkin. “Don’t volunteer any more information. Just answer the question I ask you. I know what you know, and if I want more, I’ll ask for it. If I don’t, then let it go. But don’t start expounding.”
Prosecutors warned Orkin that the two defense attorneys had already established a “good cop/bad cop” routine during the previous days of testimony. “They told me that one of the attorneys stands up, is a real sweet guy, and tries to get you to say something you shouldn’t say. Then the other guy gets up, questions your parentage and everything else to try to get you upset,” he recalled.
Orkin arrived in court in his nerd disguise and spent forty-five minutes on the witness stand answering questions for the prosecution. He detailed the elements of reverse-engineering that linked the fragment to the timer and the timer back to MEBO. Whether the technical details confused the defense attorneys or they merely discounted the importance of the science was unclear. However, after Orkin’s extensive prosecution testimony, the defense “good cop” attorney simply said, “No questions.” The “bad cop” lawyer then rose and asked a question that revealed a naïveté of technical matters.
“Isn’t it true that all electrical devices contain electronic components?”
“By definition,” Orkin answered bluntly.
No more questions followed.
By the end of the proceedings, there was no doubt that the timers originating with MEBO ended up in the hands of the Libyan government. Added to the mountain of technical evidence was the testimony of two Toshiba Corporation employees who confirmed that in 1988 Libya purchased 20,000 cassette recorders of the same model that concealed the bomb.
In all, the defense attorneys for the Libyan operatives called only three witnesses during the eighty-four-day trial. On January 31, 2001—more than thirteen years after Pan Am Flight 103 was destroyed—the three-judge panel returned a verdict: one conviction and one acquittal. The judges wrote:
The evidence, which we have considered up to this stage, satisfies us beyond reasonable doubt that the cause of the disaster was the explosion of an improvised explosive device, that that device was contained within a Toshiba radio cassette player in a brown Samsonite suitcase along with various items of clothing, that that clothing had been purchased in Mary’s House, Sliema, Malta, and that the initiation of the explosion was triggered by the use of an MST-13 timer.
The court found Abdel Basset Ali al-Megrahi, the mastermind of the plot, guilty of murder. His sentence was a minimum of twenty years’ imprisonment. His accomplice, Al Amin Khalifa Fhimah, who, authorities alleged, supplied luggage tags and assisted in getting the brown suitcase placed on the flight, was found not guilty by virtue of lack of evidence.
Terrorism moved from Scotland to sub-Saharan Africa when al-Qaeda sponsored bombings of the U.S. embassies in Kenya and Tanzania on August 7, 1998. These were immediately followed by credible reports that other embassies in Africa, Europe, and Asia were also in danger of attack. A U.S. embassy in the Balkans was identified as a specific target. As a precaution, U.S. personnel were temporarily relocated to a compound outside the city. Shortly thereafter, the local security service captured one al-Qaeda operative believed to be involved in the plotting but a second suspected member of the cell remained at large.
The at-large terrorist suspect, identified as a primary al-Qaeda forger who specialized in altered travel documents, was married to a local woman who claimed to have no knowledge of her husband’s whereabouts. His capture could produce a wealth of intelligence through the identification of the alias identities of other al-Qaeda operatives along with exemplars of their passports, driver’s licenses, and other travel documents. The death and injury suffered by U.S. officials in the Nairobi bombing added special urgency to the search. Finding the other terrorist became an obsession for the handful of case officers and techs.
OTS became involved in the hunt when the techs received word that communications had been intercepted between a suspected al-Qaeda cell in Western Europe and the Balkan terrorist. One particular exchange suggested that the European cell was providing logistical support and funds to the Balkan cell through a female cutout.
An operation combining OTS tracking and audio devices to find the terrorist was proposed. The concept involved implanting a tracking device as well as an audio transmitter in a package sent to the cutout who could be expected to deliver it to the target. Although a solid plan from the intelligence-gathering standpoint, the technical aspect was problematic.
Placing an audio and tracking device in a small package would be difficult, as both would be transmitting for an indefinite time. In addition, after the modified package was inserted into the European postal system, it would be outside of CIA control. Finally, any suspicion of the package by someone in the supply chain would alert the terrorist to his vulnerability.
Brian Mint, assigned to head the OTS tech team, understood the complexity of the operation and voiced his skepticism to the operational team. “We know he needs money,” the senior case officer insisted. “He’s gotten funds from Western Europe before and he’s looking for more. You put money in some package with tracking and audio devices and we can get him.”
Although Mint’s confidence that a technical package would work did not match that of the case officer, he assembled a team of engineers to tackle the problem. The tracking and audio devices would require a host that the target and cutout would accept without suspicion. Since money would be the bait, the package also needed to be large enough to accommodate several hundred dollars’ worth of European currency in small bills along with the two devices. In that sense, the host needed to serve as concealment for spy gear as well as money—a gift holding two secrets.
A tech was dispatched to look for suitable concealment hosts. European tourist trinkets offered the best options, since an inexpensive “gift” would not be alerting to customs officials or others handling the item during transit. The terrorist would likely assume the gift was more than it appeared based on its point of origin. Further, he would see the souvenir as a clever piece of tradecraft by his contacts and not examine the object more thoroughly once he discovered the hidden money. The psychological aspect of the “double concealment” was critical. The terrorist must have the intuitive sense to open it, but not suspect its second covert purpose.
Since cavities could be made and restored most easily in wooden souvenirs, the techs settled on a 14 by 10 by 3⁄4-inch wooden wall plaque. Mounted on the plaque’s face was a thin metallic plate engraved with the outline of an Italian cathedral and a script below reading SAINT SUSANNA.
The techs removed the metal faceplate and hollowed out a cavity in the center of the plaque large enough to hold small-denomination bills worth several thousand dollars. An Arabic linguist constructed a handwritten note: “Brother we are with you. Hopefully this will get you by until we’re able to contact you again.” The faceplate was refastened to the front of the plaque with an adhesive strong enough to hold it in place, but could be easily pried off. The techs then carved a second compartment at the edge of the plaque large enough for electronics and batteries for two weeks of continuous transmissions.
The package, addressed to the cutout, was shipped with labeling to give it the appearance of originating with the European terrorist cell. An OTS team began monitoring the tracking and audio transmissions from specially equipped vehicles.
“We didn’t know for certain where the package was going. All we knew was the address of the person we thought was the cutout,” said Mint. “If that assumption was wrong, the operation ended. Further, we didn’t know if we would be able to keep our van with the audio receiver within the transmitting distance of the bug. We did what we could and hoped for the best.”
The techs tracked the delivery to the female cutout in the Balkans. Immediately opening the package, she read the Arabic-language note and fifteen minutes later, with the package tucked under her arm, began walking across town. Tracking signals suggested she was performing a basic surveillance detection run by making several stops and doubling back on some streets. She boarded a bus that took her into one part of town, changed buses, and headed to a different section. The surveillance team, which was unobtrusively following, was eventually led to a neighborhood known for a militant Islamic presence. The cutout entered a two-story house with upper and lower apartments inside a walled compound. When she came out, she was not carrying the package.
Local security established a 360-degree perimeter around the building while the techs set up a listening post in a nearby house within range of the transmitter. An assault team assembled. The audio recorded talk among several unidentified people about the package and then sounds of the metal plate being removed from the front of the plaque. The techs and case officers wanted to cheer as the concealment passed its first test. The target had recognized that the souvenir was more than it appeared and found the cavity concealing the money.
The techs listened as an excited conversation between the terrorist and his wife was translated. The communication channel with the European cell was working. Throughout the afternoon, the techs continued to receive strong tracking signals from within the house as well as audio. In the early evening, the terrorist’s voice suddenly became agitated and his wife sounded emotional. The techs speculated that perimeter surveillance might have been spotted as the terrorist had prepared to leave the house. Then the techs heard the distinctive sound of a weapon being cleared and a round chambered.
After night had fallen and no more conversation was heard, the local operational commander directed an assault be launched. The techs listened to the commotion as the team entered the house and rushed to the second floor where the terrorist and his wife were believed to be. After a quarter hour of searching, the team reported they had not found the target.
“I thought, How could this happen? We know he was in there. We had him,” recalled Mint. “There were only two possibilities. Either he managed to slip through the security around the house or he was still in there, hiding somewhere.”
Another hour of continued searching produced nothing. The wife claimed no knowledge of the suspect’s whereabouts. Believing the operation had come to a dead end, the techs entered the house to retrieve the plaque, which they found opened underneath the bed of the second-floor apartment. Then, just as they turned toward the door to leave, pistol shots and bursts from automatic weapons fire came from the kitchen, followed by loud noises.
The assault commander had continued searching the house and entered the kitchen for a final look. Either curiosity or policeman’s instinct prompted him to move a small washing machine from against the wall. As he struggled with the surprisingly heavy appliance, a cavity between the back of the machine and the wall was exposed. At that moment the armed terrorist, who had been hiding inside the washing machine, fired a single shot that hit the commander in the chest. Another nearby officer returned fire. The terrorist rolled out of the machine and continued to shoot until he was killed with a burst of automatic fire from the assault team.
Closer inspection revealed that the working elements of the washing machine had been removed to create a hiding place just large enough for one person. Access to the concealment was obtained by removing the loosely attached tin backing and crawling through to the cavity.
Press reports the following day made no mention of the Agency’s operational or technical role in the action, though the assault team, along with the wounded commander, received deserved accolades. The OTS techs were satisfied to have played an unpublicized role in removing another terrorist from the seemingly endless war.
The six-member OTS special missions team would miss another New Year’s Day with their families. Created in the mid-1980s to provide an immediate global response to acts of terrorism, the team was prepared to deploy within hours of being alerted. Team members were trained in post-blast investigation techniques and ordnance disposal and for nearly two decades had disarmed bombs, thwarted terrorist attacks, and led foreign authorities to terror suspects. In more instances than the officers cared to remember, their urgent deployments inevitably clustered around the holiday season. Terrorists, it seemed, favored December for their murderous acts.
In 1983, American and French embassies were bombed during December, then a few days later the Provisional Irish Republican Army planted an explosive device in London’s most famous retail emporium, Harrod’s. Peruvian revolutionaries under the banner of the Tupac Amaru Revolutionary Movement took several hundred hostages at the Japanese ambassador’s Lima residence in December 1996, and the same month a suicide bomber struck during an election rally in Sri Lanka, injuring the president. Libyan terrorists bombed Pan Am Flight 103 over Lockerbie, Scotland, just before Christmas 1988. HAMAS blew up a West Bank restaurant in December 2000 and, at about the same time, a bomb in India’s Parliament killed thirteen men and women.
However, December 2001 was not like previous years. The United States was at war with al-Qaeda and its protector, the Afghan Taliban government, and the mission would take the bomb techs directly into the combat zone. Some of the team’s members came from Headquarters while others flew in from field locations. All were volunteers.
OTS designed and printed propaganda leaflets to support the 2001 war against the Taliban in Afghanistan.
Little more than two months had passed from the first October air strikes against the Taliban and al-Qaeda terrorist training camps to the liberation of the Afghan capital, Kabul. The Taliban and its al-Qaeda cohorts were clearly on the run. While some Taliban forces were surrendering en masse in Kandahar, others had taken to the hills, literally high-tailing it on horses and on foot to the White Mountain range and honeycombed cave complexes of Tora Bora.
While the large-scale military operations were all but over and the rapidly advancing forward elements of the CIA’s paramilitary units now faced only sporadic small arms fighting, the country was still far from stable. As news broadcasts showed a jubilant population defiantly enjoying activities forbidden under Taliban rule, such as kite flying and men shaving off the formerly mandatory beards, the political and security situations remained dangerously volatile.
The war itself was progressing with lightning speed and, within weeks, the Agency’s Afghanistan mission shifted from tactical support of the Northern Alliance to assuring a safe transition to a new government. The request for the OTS officers came as the Taliban abandoned control of the southern third of Afghanistan and the key city of Kandahar. The city had been among the last of the Taliban’s strongholds and concern over what unpleasant surprises might be left behind was fully justified. The need for expertise in handling explosives and skills to assess, identify, and clear buildings of IEDs and conventional munitions became imperative.
The team was given seventy-two hours to ready itself for deployment. The mission was as ambiguous as it was urgent. In reality, no one knew what the team would encounter on the ground or exactly what equipment was needed. Broadly defined, the team would provide ongoing explosive detection, assessment, and disarming capabilities for Agency and military personnel. They would be operating in areas the Taliban and al-Qaeda had controlled for years, some of it captured only days or hours earlier. They would also likely be called on to provide secondary functions, such as establishing emergency communications, field engineering, and photography.
Intelligence reports from the field described hundreds of discoveries of tons of ordnance either discarded or cached during the country’s two decades of nearly continuous warfare. This meant the team had to prepare to work with explosives of Russian, Chinese, and Pakistani origin, much of it unstable. Most would have to be destroyed to prevent it from falling into the hands of local warlords or opponents of the new government. Ironically, some ordnance and weapons were quite familiar to the OTS officers, as it came from stocks the CIA provided the Afghanistan mujahedin during their 1980s war against Soviet occupiers.
The team’s housing would be primitive and amenities such as electricity and running water scarce or nonexistent. They would live next to the native population, some of whom were deeply suspicious of the new U.S. presence or still loyal to the Taliban. Almost every Afghan man was armed. The team could expect sixteen-hour workdays that would leave them covered in dust from unpaved roads and bat guano from caves in a hot combat zone to handle unstable explosives. Nevertheless, it was the kind of job they trained and lived to do.
During an intense thirty-six hours, the team assembled enough gear, about 5,000 pounds, to sustain them for a series of operations whose length and intensity could not be known in advance. The gear they loaded into the C-17 Globemaster at Andrews Air Force base outside Washington included everything from portable x-ray devices to explosives and ammunition.
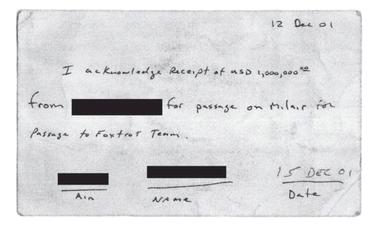
Handwritten receipt for one million dollars in cash carried in a duffel bag by an OTS officer to Afghanistan, December 2001.
As the plane’s cargo doors swung shut and the four jet engines were about to rev up, an urgent message arrived that a final package was en route. With the deadline for departure perilously close, they waited. Then an unmarked truck raced across the runway and pulled up to the plane. Lugging an ordinary-sized duffel bag from the truck, the courier presented a three-by-five card that served as a receipt for the package. “Just sign,” the courier instructed the team leader, Mark Fairbain. “You have a million in U.S. hundred-dollar bills bound in $10,000 stacks. Trust me, you don’t have time to count it.” Looking inside the bag, Mark saw stacks of bills held together by small lengths of cotton string. That was enough and he signed the receipt.
With the gear and million-dollar duffel bag secured, the plane lifted off into the night sky over Washington. Then, as the heavy transport gained altitude, the smell of burning electrical insulation filled the cavernous cargo area. The team did not argue with the pilot’s decision to divert to Charles-ton, South Carolina, rather than continue the transatlantic flight with a cargo that included a good deal of explosives.
After swapping out the two and a half tons of gear to the second plane, the team took off for another try to cross the Atlantic. “As soon as we were in the air we were off the jump seats to find a spot on the floor to get some rest,” remembered one tech. “The only problem was we had packed away the sleeping bags and ground mats. So we slept on the metal floor with just our coats draped over us.”
After an uncomfortable night, and already six hours behind schedule, they awoke in Ramstein, Germany, for a refueling stop. When airborne again, they continued on to Bahrain and from there to a secret airbase in Pakistan. Unable to make up for the six-hour delay, and with dawn breaking, the techs were informed the plane would attempt a dangerous daytime landing, the first U.S. aircraft to do so since the war began.
The southwest area of Pakistan, although not technically hostile territory, had yet to be declared completely secured. The airbase, which had first served as a launching point for search-and-rescue missions into Afghanistan, was now hosting large transport aircraft, such as C-130s and C-17s. The increasing Western presence ignited the ire of local militants whose protests included random ground fire ranging from small arms to antiaircraft guns. Pakistani armed forces found it difficult to suppress the dangerous but largely ineffective attacks.
On approach, the team strapped themselves into their seats just in case the aircraft needed to deploy countermeasures or take evasive action. The precaution, to the team’s relief, proved unnecessary and after an uneventful landing, the techs set about off-loading the two pallets of gear and rested in tents that had sprung up in the “boom town” airbase. They would make the trip to Kandahar that night under the cover of darkness.
The final leg would be a 300-mile trip from Pakistan to Kandahar in Air Force MH-53J Pave-Low helicopters. Outfitted with advanced avionics that allow flight close to the terrain’s contours, the Pave-Lows were also heavily armed with two mini-guns on the side doors and a .50 caliber machine gun mounted at the rear.
According to the plan, four Pave-Lows would fly in formation crossing into Afghanistan, then separate. Two would go to Kandahar and two to another base. Flight time was estimated at three hours, getting the team to Kandahar sometime after midnight.
Just before dark, the techs loaded the two helicopters with the two and a half tons of containers, boxes, and bags. An extensive preflight briefing covered topics ranging from landing positions to combat search and rescue (CSAR) procedures. Each team member was issued a Glock 9mm before boarding the craft.
Bad luck boarded as well. A warning light blinking in the cockpit of one Pave-Low a short time after take-off sent the OTS team back to Pakistan airbase. Once on the ground, the team reloaded their gear and million-dollar duffel bag onto a new Pave-Low, only to be told the replacement helicopter also suffered from mechanical problems. At the last possible minute for the night operation to continue, the ground crew isolated and fixed the problem.
As they lifted off from the base, the noise inside the Pave-Low drowned out conversation. Gunners positioned themselves at the opened side doors and the back ramp was opened for the .50 cal gunner. Crossing into Afghanistan, all three gunners opened up and test fired. Adding to the noise, the opened doors created an uncomfortable internal wind tunnel. “Only then,” recalled Mark, “did we learn what a cold rough flight really was, when the helicopter began bouncing up and down from the wind of the southern mountain range.”
Three hours later, the chopper hovered over bomb craters and debris before touching down on a dark runway of what was once a state-of-the-art airport. Built in the 1970s, Kandahar International Airport was at one time the largest and most modern in Central Asia, but it had been severely damaged in the Russian invasion in the early 1980s. After the Soviets left, the airport became a stronghold for Taliban and al-Qaeda forces, which turned its runways into minefields. Recent U.S. bombing raids had added to the destruction, pockmarking the tarmac with deep craters and littering it with the debris of war. Now, with the airport recaptured by U.S. Marines and Pashtun guerillas, control of the once modern structure—less than twenty miles outside Kandahar—signaled the end of the Taliban’s fixed presence in the area.
With the chopper’s blades still turning, the team rushed to off-load the gear in the fifteen minutes the pilot allowed before taking off for the return flight to Pakistan. No reception committee greeted the six as the Pave-Low vanished into the night, leaving the team alone on the darkened runway at four o’clock in the morning. The team stood beside thousands of pounds of high-tech equipment and the money bag they had hauled from plane to plane and chopper to chopper, used en route as a pillow, footrest, and bed. Mark noticed that the strings securing the stacks of hundred-dollar bills had come untied leaving a bag filled with 10,000 loose bills.
Armed with only Glock 9mm sidearms, the team had no choice but to wait in the open on the runway. “We had been told that the Marines moved onto the airfield a few hours before, but they were nowhere to be seen,” recalled a team member. “We had no contact plan. Six sets of headlights suddenly popped up at about three hundred meters and headed our way. We hoped they were friendlies.” The headlights were from vehicles belonging to two Marine units supported by Delta Force operators.
The Marines greeted the OTS team in short-bedded Toyota pickups woefully inadequate for hauling 5,000 pounds of equipment to the Governor’s Palace in downtown Kandahar. Two trips would be necessary, the trip taking an hour each way.
The palace compound had until recently been home to the Taliban’s reclusive one-eyed spiritual leader Mullah Omar. A chief architect of Taliban rule, Omar had issued the religious decrees that turned Afghanistan into a repressive regime that provided a sanctuary to Osama bin Laden and the al-Qaeda terrorists. The complex consisted of two large parallel buildings, one the residence and the other the meeting hall/auditorium, with a courtyard between them and narrow walls at each end to create an enclosed rectangle.
The team once more transferred the gear, this time into the palace. The nearly three-day trip had left them exhausted and sleep was a priority. However, not four hours later Mark was awakened with urgent news. A man claiming to have important information had come into the courtyard telling a story about explosives buried within the palace. Fighting grogginess and working through an interpreter, Mark engaged the slightly built man dressed in tunic and turban.
Speaking in a calm, deliberate voice the volunteer explained that the retreating Taliban hid explosives in the palace’s earthen roof. The explosives, he said, were to be detonated just after sundown that day, at the start of the Muslim holiday of Eid al-Fitr, the three-day celebration marking the end of Ramadan.
The walk-in seemed credible—so credible that Mark could not suppress the suspicion that he had helped plant the explosives and was now having second thoughts. With the fall of the Taliban, loyalties in the country were shifting daily. The volunteer, who spoke matter-of-factly about explosives possibly only a few meters above their heads, would not have been the first Taliban loyalist to switch sides.
Inside the palace, everything seemed normal with the American and British troops and Afghanis, all involved in their own tasks. More than fifty people were already present, preparing for the Eid festivities, and within hours the assembly hall would be filled with the principal leaders of the southern third of Afghanistan, guests of the new governor, Gul Agha Sherzai, who was hosting the event.
For experienced OTS officers who had picked through many post-blast scenes, it was easy to imagine the sudden death and destruction from a rooftop blast. Destroying Afghanistan’s southern leadership on a Muslim holy day would be a cruel, audacious act and a devastating blow to the new government and the United States. Delay could prove fatal to the local officials and guests, more than a hundred U.S., Australian, and British military personnel, as well as America’s Afghan policy.
Within fifteen minutes of the conversation, Mark made the decision to send one member of the team to the roof. Putting an officer on the roof in daylight was risky. If the building was under surveillance, anyone on the roof was certain to be spotted and a terrorist could decide to detonate ahead of schedule. Mark calculated the risk, taking into account the approaching nightfall and the start of Eid. Both were less than four hours away.
Frank Shumway, a tech experienced in using thermal imaging equipment, was rousted from a sound sleep. After Mark explained the situation, Frank agreed to climb onto the roof. Strapping on a hundred pounds of equipment, including communications gear to keep him in constant contact with the team, Frank would report each movement and every observation. These transmissions would be recorded, and should a detonation occur, by accident or command, the recorded information could provide valuable data for post-blast investigators and future operations.
After navigating the narrow ledge of the perimeter wall that joined the two buildings, Frank climbed a ten-foot ladder to reach the earthen roof above the palace’s assembly hall. Its smooth and hard packed surface showed no signs of recent disturbance, but as soon as he switched on the thermal imager, the results immediately contradicted everything Frank saw through his own eyes.
The small screen identified four distinct “hot spots,” each giving a signature of recent excavation. What the human eye cannot see registered clearly on the screen. No matter how well a recently dug hole is refilled and disguised, it will absorb heat at a different rate than an undisturbed area. Foreign objects just below the surface—such as IEDs—can also enhance the thermal signature.
“Four holes are set in an L-shape; one hole is positioned directly above the reception area and the three others run along the lateral axis of the primary assembly hall,” Frank reported. “The imaging also shows a narrow line of disturbed earth from hole to hole, then off toward the edge of the building.”
Frank’s information bolstered the credibility of the walk-in’s report. Should the holes contain even a moderate amount of explosives, the blast would, at minimum, collapse the roof. While the imager could not provide clues to what, if anything, was beneath the surface, the pattern, size, and shape of the hot spots were consistent with what was known of how mines or munitions could be deployed. If the holes concealed an explosive array, the work had been extraordinarily well done.
Satisfied that the roof had been thoroughly imaged and convinced that explosives were likely buried there, Mark recommended to the U.S. officer in command that military personnel and the Afghanistan locals preparing the celebration be ordered to the far side of the compound. The soldiers complied, but the Afghanis declined to evacuate or even suspend their preparations. It was only two hours before dark and guests had already begun to arrive in the reception area.
With the most experience in explosive ordnance disposal of any member of the team, Mark made the next foray onto the roof to probe the hot spots. Information from the walk-in, combined with the hole patterns and a narrow line of disturbed earth running from the holes to the edge of the roof all strongly suggested the explosives were configured in a command detonated array. With command detonation, the four connected charges would be set off with a single signal. Working with the command detonation hypothesis the team prepared a small electric charge to cut the command wire.
The potential for disaster was enormous. The team still had no idea what type of IEDs lay buried inches beneath the surface, whether there was a secondary detonation system, or if they were booby-trapped.
As the reception hall rapidly filled with Afghan dignitaries and nightfall approached, Mark took the narrow staircase to the roof and began gently probing around the areas shown on the imager. Several inches underground, his probe hit what felt like steel. He carefully swept the crumbled earth away to expose a small section of the buried object. Using the thermal images as a road map, he continued working slowly and cautiously, and eventually identified an eight-gauge detonator lead wire buried just beneath the surface that connected the four holes and led off to join a tangle of other communications and electrical wires that fed the building from the outside. He had seen enough. There were several explosives beneath the roof linked for command detonation with the signal wire trailing off to some remote place in the war-battered city beyond the compound. He attached the electric cutting charge, gave the signal, and the line was severed.
Mark left the roof just as the sun was setting. Afghan dignitaries were now crowded into the reception hall of the palace oblivious to what was likely thousands of pounds of live explosives only a few feet above their heads. The end of Ramadan was announced as Mark made his way down the narrow staircase and a liberated Kandahar erupted in celebratory gunfire. He could not suppress a smile at the thought that somewhere among the city’s celebrants was a terrorist, his finger repeatedly pushing a button in vain, wondering why in the name of Allah his best efforts had come to naught.
There had not been time to consider removing whatever munitions lay buried beneath the surface. The palace compound was as secure as possible and Mark reasoned that leaving the munitions buried until the end of Eid carried little risk.
After Eid, an Afghan military de-mining team was brought onto the compound to dig the ordnance out of the roof. Mark estimated that it would take one day per hot spot—four days in all—to safely excavate the explosives. With the Afghan squad assembled, two OTS team members began a four-hour refresher course in explosive ordnance disposal (EOD) procedures and safety. The introductory remarks were never concluded. The senior Afghan officer interrupted to announce that his troops were well prepared for this type of work. No further training was necessary. It was the shortest refresher course in OTS history.
The OTS team watched at a distance as the Afghanis attacked the job with frightening enthusiasm. What Mark had estimated as a four-day job was finished in less than one. Before the day ended, the Afghanis had removed more than 2,200 pounds of hard case explosives, including fifty-five 122mm tank rounds and more than a hundred antitank mines from the four hot spots. A fifth hot spot turned out to be empty.
The rooftop IED would be classified as rudimentary, but what it lacked in sophistication, it compensated for in size. Detonation would have reduced the palace to rubble, killing or injuring everyone inside, and in all likelihood taking out the U.S.-occupied structure across the courtyard.
“We’ve heard a dozen times from our paramilitary colleagues and the special ops guys that our entire deployment was paid for in full that first day,” noted a team member.
A few days later, with the components of the bomb piled up outside the palace as a photo op, the local commander called a press conference to announce the find and the successful defusing. A single bored reporter, along with a photographer, listened politely and took notes, but no story ever appeared.
The walk-in was invited back to the palace to receive a reward. Afghan and U.S. personnel staged a semiformal ceremony. After drinking his tea, he was given $1,000 in hundred-dollar bills. He showed little reaction to the reward money, which he accepted graciously, and then offered a short speech, declaring that his only motivation was to help his country.
The OTS team remained in Afghanistan for another six weeks, clearing hundreds of tons of ordnance from homes and remote hideaways. While hiking the rugged White Mountain range with Delta Force operators, they discovered caches of aging explosives crammed into the man-made caves. In one cave, stockpiles of mortars and mines were packed from floor to ceiling, extending far back into the mountains. A B-52 bombing strike was required to detonate the massive cache.
On the outskirts of Kandahar, in the rubble of an al-Qaeda training camp, the team discovered and then destroyed dozens of drums of chemicals used to produce the explosive known as triacetone triperoxide, or TATP. A favorite of suicide bombers, TATP was used by would-be shoe-bomber Richard Reid in his foiled attempt to bring down an airplane in December 2001, and again by terrorists in the July 2005 London bombings. The number of lives they saved may never be known.
Upon their return to the United States, members of the team were awarded the CIA’s Intelligence Star for Valor in a ceremony presided over by DCI George Tenet. They became members of an elite cadre of some twenty techs whose courage and service has earned the honor of receiving the Intelligence Star during the fifty-year history of the Office of Technical Service.